OPS235 Lab 7 - CentOS7
Contents
LAB PREPARATION
Purpose / Objectives of Lab 6
In this lab, you will learn how to use the ssh, scp, sftp commands to work between computer systems via a network. In addition, you will learn various methods of how to communicate between computer networks using SSH tunneling, and simplify secure network communication by using Public Key Authentication.
Main Objectives
- To set up, configure Secure Shell Services (ssh/sshd)
- To use the ssh, scp, and sftp clients to access another host securely
- Use ssh to tunnel X applications
- Use ssh to tunnel other traffic
- To customize sshd to create a more private, secure system
Minimum Required Materials
My Toolkit (CLI Reference)
| Networking Utilities | Additional Utilities: | Configuration Files: |
INVESTIGATION 1: CONFIGURING AND ESTABLISHING AN SSH CONNECTION
Part 1: Enabling the sshd service.
- Use your c7host machine to complete this section
- OpenSSH should have been installed by default. Lets confirm this by issuing the command:
rpm -qa | grep ssh - You should see a number of packages installed including
openssh-clientsandopenssh-server -
openssh-serverinstalls a service calledsshd, confirm this service is running by issuing the command:service sshd status - Now check that the sshd service is configured to start automatically:
chkconfig --list sshd - Now that you know the service is running investigate what port number and protocol sshd uses by issuing the command:
netstat -atunp - What protocol and port is the sshd process using?
- What is the state of the port?
- Why do UDP ports not have a state?
- Reissue the
netstatcommand without thenoption. - What is the difference? How is the file /etc/services related to the difference?
-
netstatis a very useful command for anything to do with networking. Read its man page and make sure you understand its output. - Make sure your
sshdservice is running on all 3 of your VM's
Answer Part 1 observations / questions in your lab log book.
Part 2: Establishing an ssh connection.
- Use your centos2 VM to complete this section.
- Establish an ssh connection to your centos3 VM using the command:
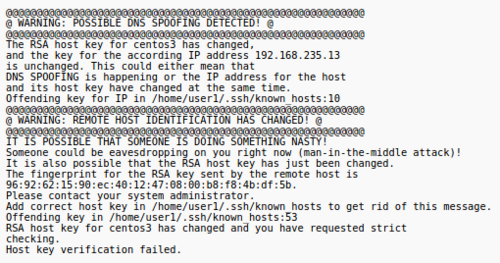
ssh ops235@centos3(Where 'ops235' is the account on centos3 and 'centos3' is the hostname of the centos3 VM.) - You should receive a message similar to the following:
- The authenticity of host 'centos3 (192.168.235.13)' can't be established.
- RSA key fingerprint is 53:b4:ad:c8:51:17:99:4b:c9:08:ac:c1:b6:05:71:9b.
- Are you sure you want to continue connecting (yes/no)? yes
- Warning: Permanently added 'centos3' (RSA) to the list of known hosts.
- The authenticity of host 'centos3 (192.168.235.13)' can't be established.
- Answer yes to add to the list of known hosts.
- Logout of your ssh connection by typing
exit. - Check the state of the connection after logging out. Wait a few minutes and then check again. Record your observations.
- Make certain to exit all connections, and that your shell is located in your centos3 server. You can verify this by entering the command:
hostname - Use the Internet to search for "TCP 3 way handshake" to see how TCP connections are established and closed.
Answer Part 2 observations / questions in your lab log book.
Part 3: Establishing an ssh connection using Public Key Authentication.
- Start by generating a keypair as your learn account on centos2 using the command:
ssh-keygen - That should generate output similar to the following:
Generating public/private rsa key pair. Enter file in which to save the key (/home/user1/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/user1/.ssh/id_rsa. Your public key has been saved in /home/user1/.ssh/id_rsa.pub. The key fingerprint is: 93:58:20:56:72:d7:bd:14:86:9f:42:aa:82:3d:f8:e5 user1@centos2
- After generating the keys it prompts you for the location to save the keys. The default is
~/.sshYour private key will be saved asid_rsaand your public key will be saved asid_rsa.pub
- Now issue the command
ssh-copy-id -i ~/.ssh/id_rsa.pub centos3 - Now we can ssh into centos3 from centos2 using two different authentication methods.
- Make certain to logout of your centos3 system. Use the
hostnamecommand to verify you are back in your centos2 server.
Answer Part 3 observations / questions in your lab log book.
INVESTIGATION 2: USING SSH AND OTHER SECURE SHELL UTILITIES
Part 1: How do you use scp and sftp.
- To connect to a remote host type the command:
sftp ops235@centos3 - This will establish an interactive session after authentication.
- Type
helpto see the list of sftp commands at any time. - The 2 main commands are
putto copy a file from the local host to the remote host (upload) andgetto copy a file from the remote host to the local host (download). - Try using
sftpto transfer files back and forth between hosts. - As you did previously you can also use the
scpcommand to copy files to and from remote hosts and even from one remote host to another. - Use
scpto copy your services file to the centos3 host into the /tmp directory. (The path on a remote host follows the :) using the command:scp /etc/services ops235@centos3:/tmp - Experiment with
scpto copy a file from centos3 directly to centos1.
Answer Part 1 observations / questions in your lab log book.
Part 2: How do you use ssh to tunnel X.
You can also use ssh to tunnel window and bitmap information. Allowing us to login to a remote desktop host and run a Xwindows application such as gedit or firefox and the application will run on the remote host but be displayed on the local host.
- From centos2
sshto centos1 using the following command:ssh -X -C user@centos1(Where 'user' is your learn account on centos1). The-Xenables the forwarding of X window information, and the-Cenables compression for better performance. - Once connected run the
geditapplication. (Gnome Text Editor) - The gedit window will display on centos2 but it is running centos1.
- Enter some text and save a file with
gedit. - Exit
gedit. - Where was the file saved?
- Experiment with running other GUI applications through
ssh.
Answer Part 2 observations / questions in your lab log book.
INVESTIGATION 3: SECURING THE SSH CONNECTION
Investigation 6: How do you use ssh to tunnel other traffic.
- You will be working with the 2nd scenario of bypassing a firewall that blocks http traffic.
- In this investigation centos1 will be your http server and centos2 will be your client.
- On the HTTP server make sure the Apache web server is installed by typing the command:
rpm -q httpd - If it is installed check the configuration of the service to see if it is automatically started at any runlevels by using the
chkconfig hcommand. - If it has not been started automatically start the service using the service command.
- Confirm that httpd is listening to TCP/80 using the netstat command.
- Create a small html document called
/var/www/html/index.htmlthat displays a short message.* - On the centos1 (the http server) confirm everything is working locally by using a browser to connect to http://localhost
- Set the default firewall configuration on centos1 to REJECT incoming requests to http (TCP/80)
- Confirm that you can't connect by using firefox on centos to connect to centos1 http://centos1/
- On centos2 confirm that the httpd service is stopped so it cannot interfere with your observations.
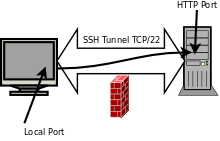
- The next step is to establish a tunnel. When you establish a tunnel you make an ssh connection to a remote host and open a new port on the local host. That local host port is then connected to a port on the remote host through the established tunnel. When you send requests to the local port it is forwarded through the tunnel to the remote port.
- Establish a tunnel using a local port on centos2 of 20808, that connects to the remote port on centos1 of 80, using the following command on centos2:
ssh -L 20808:centos1:80 user@centos1
- Once the tunnel is established use netstat to verify the port 20808 is listening on centos2
- Now using the browser on centos2 connect to http://localhost:20808
- You should see the index.html page on centos1.
- Close the ssh connection and verify that the port 20808 is no longer listening.
Answer the Investigation 6 observations / questions in your lab log book.
Investigation 7: How do you make sshd more secure
- Think of a good quality password and change your root passwords on all 3 VM's to be more secure. (It would be a good idea to do this for non-root accounts also)
- The next change you can make is to prevent the root account from logging in to sshd altogether.
- Edit the file
/etc/ssh/sshd_configand look for the optionPermitRootLogin. Uncomment the option (or add the option if it does not appear) and change the option value to"no". - Even better, it is possible to restrict access to just specific users that require it.
- Edit the file
/etc/ssh/sshd_configand add a new option of"AllowUsers account"using your login account for account. - In order for these changes to be effective, issue the following command to restart the sshd service:
service sshd restart - Now any hacking attempt also has to guess an account name as well as the password. If you need to ssh with root access, ssh as a regular user and use
su -to become root. - Next change the default port number that sshd uses (TCP:22).
- Edit the sshd configuration file again and change the port number it uses to 2200.
- Restart the service.
- Confirm the new port is being used with a
netstatcommand. - Before we can use this new port we must change our firewall to allow traffic through the new port number and block access to port 22:
iptables -I INPUT -p tcp -s0/0 --dport 22 -j DROPiptables -I INPUT -p tcp -s0/0 --dport 2200 -j ACCEPT - To test the new port connect to centos1 from centos2 using the following command:
ssh -p 2200 user@centos1
- Finally as a system administrator you should periodically monitor your system logs for unauthorized login attempts.
- On CentOS systems the log file that is used is
/var/log/secure - It also logs all uses of the
suandsudocommands. - Attempt to connect to all of your VM's as root and other users using both public key and password authentication. Use some su and sudo commands also.
- Inspect the log to see what kind of information is logged.
Answer the Investigation 7 observations / questions in your lab log book.
Completing the lab
Arrange proof of the following on the screen:
- have configured sshd to allow connections over a non default port.
- have logged in to a VM using public key authentication
- have scp'd and sftp'd files to a VM.
- have tunneled Xwindows applications through ssh
- have tunneled http through firewall using ssh
- have secured ssh against root access
Preparing for Quizzes
- What port does sshd use by defaults?
- What file is used to configure sshd?
- What sftp commands are used to upload/download files?
- What kind of files are stored in the "~/.ssh/" directory?
- How do you determine whether the sshd service is running on your system or not?
- What is the purpose of the ~/.ssh/known_hosts file?
- What is the purpose of the ~/.ssh/authorized_keys file?
- Which system log file records each use of the sudo command?
- How do you stop the sshd service?
- How do you tunnel XWindows applications?
- What port is the default scp port?
- What port(s) is/are used by httpd service?