OPS235 Lab 6
Contents
- 1 LAB PREPARATION
- 2 INVESTIGATION 1: CONFIGURING A VIRTUAL PRIVATE NETWORK (VPN)
- 3 INVESTIGATION 2: MANAGING YOUR NEWLY-CREATED NETWORK
- 4 LAB 6 SIGN-OFF (SHOW INSTRUCTOR)
- 5 Practice For Quizzes, Tests, Midterm & Final Exam
LAB PREPARATION
Purpose / Objectives of Lab 6
In this lab, you will learn the basics of networking by using your Virtual Machines and your c7host machine. You will first set up a virtual private network among those machines. In addition, you will learn to set up network names (to associate with server's IP Addresses), associate network services with port numbers for troubleshooting purposes, and setup firewall policies via the iptables command.
Main Objectives
- Configure a private (virtual) network for your VMs and your c7host machine
- Configure network interfaces for your Virtual Machines using both graphical and command-line utilities.
- Use local hostname resolution to resolve simple server names with their corresponding IP Addresses
- Use common networking utilities to associate network services with port numbers for troubleshooting purposes
- Gain initial exposure to the iptables command used to configure and maintain a firewall for protection and troubleshooting
- Configure iptables to allow/disallow/forward different types of network traffic
| Minimum Required Materials |
Linux Command Reference | |||
|
|
Networking Utilities ifconfig |
Additional Utilities | ||
INVESTIGATION 1: CONFIGURING A VIRTUAL PRIVATE NETWORK (VPN)
For the remainder of this course, we will focus on networking involving our VMs and our c7host machine. This lab will focus on setting up a virtual private network (VPN), connecting our VMs and c7host machine to the VPN, and configuring our VPN to make more convenient to use, troubleshoot and protect. Lab 7 will focus on configuring SSH and making access to the VPN more secure. Finally, lab 8 will focus on configuring the network for fixed workstations, mobile devices, or both at the same time.
There are several reasons for creating VPNs. The main reason is to safely connect servers together (i.e. to safely limit but allow share information among computer network users). This allows for a secure connection of computers yet controlling access to and monitoring (protecting) access to permitted users (discussed later in lab7).
Part 1: Configuring a Private Network (Via Virtual Machine Manager)
If we are going to setup a private network, there are a number of steps to perform: First, define a new private network in the Virtual Manager application; and second, configure each of our VMs to connect to this new private network. In Part 1, we will be perform the first operation. In part 2, we will be performing the second operation for all VMS (graphical and command-line).
Before configuring our network we want to turn off dynamic network configuration for our Virtual Machines by turning off the "default" virtual network. We will then define our virtual private network.
Perform the following steps:
- Launch your c7host VM and start the Virtual Machine Manager.
- Make certain that the centos1, centos2, and centos3 virtual machines are powered off.
- In the Virtual Machine Manager dialog box, Select Edit-> Connection Details.
- In the Connection Details dialog box, select the Virtual Networks tab
- Click to deselect the Autostart (on boot) check-box options and click the Apply button.
- Then stop the default network configuration by clicking on the stop button at the bottom left-side of the dialog box.
- Click the add button (the button resembles a "plus sign") to add a new network configuration.
- Type the network name called: network1, and then click the Forward button.
- In the next screen, enter the new network IP address space called: 192.168.235.0/24
- Disable the DHCP4 check box and click the Forward button.
- Click the Forward button to accept the default in the next screen.
- Enable Network Forwarding by Selecting Forwarding to physical network, the destination should be Any physical device and the mode should be NAT
- Proceed with changes, and click Finish.
- We will now reconfigure each of our VMs to use our new virtual network network1
- Let's start with our centos1 VM. Double-click on your centos1 VM, but instead of running the VM, click on the view menu, and select: Details
(Note: the Virtual Machine window will appear - do not start virtual machine) - In the left pane of the Virtual Machine window, select NIC: and note that this NIC is on the "default" virtual network
- Change it to Virtual Network network1: NAT (i.e. the VPN that you just created) and click the Apply button.
- Let's start with our centos1 VM. Double-click on your centos1 VM, but instead of running the VM, click on the view menu, and select: Details
Part 2: Configuring Network For centos1 VM
In this section, we will be using a graphical tool to connect our centos1 and centos2 VMs to our private network.
Perform the following steps:
- On your c7host machine, run ifconfig and make note of the IP address assigned to the virbr1 (i.e. "Virtual Bridge) interface. This will be the default gateway and DNS server for your VMs.
- Start your centos1 VM and login.
- Within your centos1 VM, click Applications menu, then select System Tools, and then Settings.
- In the Settings Dialog Box, click on the Network icon.
- For the Wired connection, click the settings button (The icon appears as a gear located at the bottom right-hand corner of the dialog box).
- Select the IPv4 tab. Change Address from Automatic (DHCP) to Manual.
- In the Addresses section, enter the following information:
- IP Address: 192.168.235.11
- Subnet Mask: 255.255.255.0
- Default Gateway: The IP address of virbr1 on your centos host.
- Click on the DNS' field and add The IP address (virbr1 on your centos host) as the primary DNS server.
- When finished, check your settings, and then click the Apply button.
- Open a terminal and issue the ifconfig command to confirm the IP ADDRESS settings change.
- Verify that centos1VM is now connected to the VPN by issuing the following command from your c7host machine:
ping 192.168.235.11 - Switch to your centos2 VM.
- Run the network configuration tool and enter the following static configuration for your centos2 VM:
- IP Address: 192.168.235.12
- Subnetmask: 255.255.255.0
- Default Gateway: 192.168.235.1
- DNS Server: 192.168.235.1
- When finished, click Apply and close the network dialog box.
- Issue the ifconfig eth0 command to verify your new settings.
- Issue the command:
ping 192.168.235.1to confirm that you can connect to your c7host VM. - Switch to your c7host VM, and issue the command:
ping 192.168.235.11to confirm that you can connect to your centos1 VM.
Part 3: Configuring VM Network Setup via Command Line (centos3)
The centos3 and centos2 VMs are text-based only systems, thus we cannot use a graphical tool to configure centos3 to connect to our private network. Therefore we will learn how to perform this task by using command-line tools.
Perform the following steps:
- Configure the centos3 VM (in the View -> Details menu of Virtual Machine Manager) to configure the NIC interface to network1 (refer to Part 1)/
- Start your centos3 VM, login, and su to root.
- Use the command called: ifconfig to list active interfaces, you should see one with a name of eth0 or a similar name.
- To configure your card with a static address use the following command:
ifconfig eth0 192.168.235.13 netmask 255.255.255.0
- To configure a default gateway for that interface enter the command:
-
route add default gw 192.168.235.1
-
- To configure a DNS server for this VM, edit the file /etc/resolv.conf. Change the nameserver line to read:
- nameserver 192.168.235.1
- Save your editing session.
- Confirm your settings work by doing the following (you might need to do the steps 3 and 4 a few times before it works; keep checking with the commands below and wait a bit before each attempt):
-
ifconfig route -n-
ping(your other VM's and c7host) -
ssh( to your Seneca's Matrix account to test your DNS)
-
- Restart the
centos3VM, or just wait a few minutes. - Login and test your configuration again. What happened?
- While we can configure network settings from the command line those settings are not persistent. To configure persistent network configurations we need to edit the configuration files.
- Change to the /etc/sysconfig/network-scripts directory
- List the contents of this directory. You should see 2 different types of files, network config scripts and network configuration files.
- Look for the configuration file for your original interface, it should be named ifcfg-eth0
- Edit the new file for you interface and give it the following settings (or create a brand new file, might be easier than editing the old one):
- DEVICE="eth0"
- IPADDR="192.168.235.13"
- NETMASK="255.255.255.0"
- GATEWAY="192.168.235.1"
- HWADDR="52:54:00:3f:5c:fa" <-- DO NOT COPY THIS VALUE! Use MAC address for YOUR interface using:
ifconfig eth0 - DNS1="192.168.235.1"
- BOOTPROTO="static"
- ONBOOT="yes"
- NM_CONTROLLED="yes"
- IPV6INIT="no"
- Save the file and then restart the network connection by issuing the commands:
ifdown eth0andifup eth0 - Verify your configuration as you did before.
- Restart the centos3 VM.
- Use the ifconfig and ping commands to verify your network connection to other VMs.
- Login and attempt to ssh to your matrix account to verify the settings.
We need to also configure your centos2 VM for a persistent network connection as well: - Configure the centos2 VM (in the View -> Details menu of Virtual Machine Manager) to configure the NIC interface to network1 (refer to Part 1)/
- Start your centos2 VM, login, and su to root.
- Use the command called: ifconfig. You should see an error that the command does not exist. Actually, the "ifconfig" is deprecated, and is being replaced by the command: ip address.
- Issue the command:
ip addressand write down MAC address for your eth0 network interface. - Edit the /etc/sysconfig/network-scripts/ifcfg-eth0 file using the IPADDR and MAC address for you centos2 VM.
- Save changes, and issue the ip address and ping commands to verify that you can connect to other VMs on your network.
Answer INVESTIGATION 1 observations / questions in your lab log book.
INVESTIGATION 2: MANAGING YOUR NEWLY-CREATED NETWORK
Connecting a private network is an important task, but a system administrator also needs to manage the network to make it convenient to use, make it safer from unauthorized access, and troubleshoot network connectivity problems.
This investigation will expose you to useful "tweaks" and utilities to help accomplish this task. Lab 7 requires that you understand these concepts and have a good general understanding how to use these troubleshooting utilities (like netstat and iptables).
Part 1: Using /etc/host File for Local Hostname Resolution
After setting up a private network, it can be hard to try to remember IP addresses. In this section, we will setup your network to associate easy-to-remember server names with IP ADDRESSES.
Perform the following steps:
- Complete this investigation on all of your VMs and the c7host machine.
- Use the
hostnameandifconfigcommands on your c7host machine and all of your 3 VM's to gather the information needed to configure the /etc/hosts file on all of your Linux systems. - Edit the /etc/hosts file for the c7host, centos1, centos2 and centos3 VMs. Add the following contents to the bottom of the /etc/hosts file:
- 192.168.235.1 c7host
- 192.168.235.11 centos1
- 192.168.235.12 centos2
- 192.168.235.13 centos3
- Verify that you can now ping any VM by their hostname instead of the IPADDR.
Part 2: Using Arrays to Collect VM Network Information
We finish shell scripting by using arrays by reading and storing networking information for each VM (centos1, centos2, and centos3) to be stored in a report in your c7host machine. We will use the ssh command in order to grab the network information (one VM at a time), and store the network setup into an Associative array in our c7host machine.
If you do not entirely understand the script that you will enter, just realize that we are using these "special storage variables" in order to make this work.
Perform the following steps:
- Perform this section in your c7host machine.
- Open a shell terminal and login as root.
- Change to the /root/bin directory.
- Using a text editor, create a Bash shell script called network-info.bash and enter the following content below:
#!/bin/bash
# Author: *** INSERT YOUR NAME ***
# Date: *** CURRENT DATE ***
#
# Purpose: Creates system info report
#
# USAGE: ./network-info.bash [file-pathname]
if [ $USER != "root" ] # only runs if logged in as root
then
echo "You must be logged in as root." >&2
exit 1
fi
if [ $# -ne 1 ]
then
echo "You need to provide a file-pathname" >&2
echo "USAGE: $0 [file-path-name]" >&2
exit 0
fi
- We will now use a while loop to read every line in the network configuration file and store into an array as a separate array element. Add the following content to your shell script editing session:
while read line
do
network[$index]="$line"
index=$(($index+1))
done < $1
- Finally, we will generate a web-page document, use a loop to printout the results of the data (stored in an array) and open the web-page document in the firefox web-browser.
cat > /root/network-info.html <<+
<!DOCTYPE html>
<html>
<head>
<title>Network Information</title>
</head>
<body>
<h3>Network Information for: $1</h3>
<table cellpadding="5" cellspacing="0" border="1">
+
for((x=0; x<$index; x++))
do
echo "<tr><td>${network[$x]}</td></tr>" >> /root/network-info.html
done
cat >> /root/network-info.html <<+
</table>
</body>
</html>
+
/bin/firefox /root/network-info.html
- Give this shell script execute permissions and run this shell script. What do you notice from the report that the shell script generated?
- The the wget command to download, set permissions and run the following script to see the usefulness of arrays: URL
|
Part 3: Network Connectivity & Network Service Troubleshooting Utilities
Troubleshooting network problems is an extremely important and frequent task that a Linux/Unix system administrator performs on a daily basis! Since network services (such as file-server, print-servers, web-servers, and email-servers) depend on network connectivity, as Linux/Unix sysadmin must be able to quickly and effectively pin-point sources of network problems in order to resolve them.
Network service problems may not be entirely related to a "broken" network connection, but a service that is not running or not running correctly. The following table lists the most common listing of utilities to assist with detection of network connectivity or network service problems to help correct the problem.
Perform the following steps:
- Switch to your c7host machine.
- Issue the ping command to test connectivity to your centos1, centos2, and centos3 VMs.
- Examine the contents of the ARP cache by using the command:
arparp What is the purpose of ARP? - Check the contents of the cache again by using the command:
arp -nWhat was the difference in output? - Issue the following command:
netstat -atThis command will list all active TCP ports. Note the state of your ports.
TCP is a connection oriented protocol that uses a handshaking mechanism to establish a connection. Those ports that show a state of LISTEN are waiting for connection requests to a particular service. For example you should see the ssh service in a LISTEN state as it is waiting for connections.
- From one of your VM's login to your host using ssh.
- On your c7host VM rerun the
netstat -atcommand and in addition to the LISTEN port it should list a 2nd entry with a state of ESTABLISHED. This shows that there is a current connection to your ssh server. - Exit your ssh connection from the VM and rerun the command on the CentOS host. Instead of ESTABLISHED it should now show a state of CLOSE_WAIT. Indicating that the TCP connection is being closed.
- On your c7host VM, try the command:
netstat -atnHow is this output different? Without the -n option netstat attempts to resolve IP addresses to host names (using /etc/hosts) and port numbers to service names (using /etc/services) - Examine the /etc/services file and find which ports are used for the services: ssh, sftp, http
- Now execute the command netstat -au What is the difference between the options: -at and -au? When examining UDP ports why is there no state?
Using Firewalls in Linux (iptables)
Since Linux servers may be connected to the Internet, it is very important to run a firewall to control what comes into the computer system, what goes out of the computer system, and what may be forwarded to another computer. A utility called iptables can be used to set the firewall rules on a Linux server.
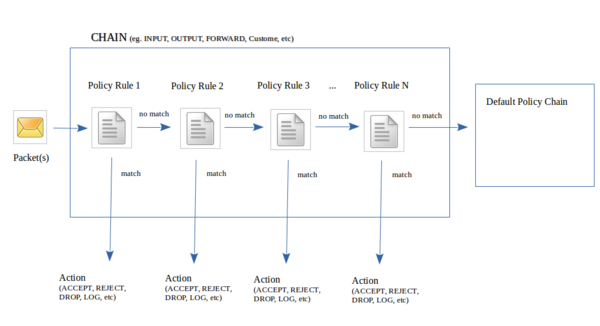
Basically, there is a list (chain) of policy rules that packets must pass-through in order to handle packets. If a packet matches a rule, then an action is taken (some examples include: ACCEPT, DROP, REJECT, or LOG). If the packet passes through the chain of rules without a match, then the packet is directed to the default policy chain (for example: ACCEPT, REJECT, or DROP).
You can create your own customized chains (which you will learn in OPS335 course) but to keep thing simple, we only deal with 3 common predefined chains:
- INPUT: Packets coming into current Linux server
- OUTPUT: Packets leaving current Linux server
- FORWARD: Packets being routed between Linux servers
Perform the following steps:
- For the remainder of this section, use your c7host machine.
- Issue the following command to list the existing iptables policy rules:
iptables -L. - Were there already iptables policy rules that already existed by default?
- Issue the following command to reset the iptables policy rules:
iptables -F. - Issue the iptables -L command to verify that the iptables rules have been reset.
Setting Default Policy and Policy Exceptions with iptables
Usually when setting policy rules with iptables, a general "overall" policy is set (default policy chain), and then set policy rules in other chains which act as exceptions to the default policy. Usually, a general policy would apply to ALL types of packets (tcp, udp, icmp) and all communication port numbers (80, 22, etc).
The option -P is used with the iptables command to set a default policy chain.
Examples:
| iptables -P INPUT DROP | Set default policy to drop all incoming connections for ALL protocols, ALL communication ports, ALL IP addresses |
| iptables -P OUTPUT DROP | Set default policy to drop all outgoing connections for ALL protocols, ALL communication ports, ALL IP addresses |
After the overall default policy is set, then you can create policy rules that are "exceptions" to the default policy rules. The -j option is used to redirect (jump) packets to actions (ACCEPT, REJECT, DROP, LOG) if the packet match that policy rule. The option -p will indicate the protocol used (eg. tcp, upd, icmp). The options --dport or --sport indicate the "destination communication port" or "source communication port" respectively. You can view the file /etc/services to determine the communication port number for the appropriate network service. The option -A is used to append the policy rule to the bottom of the chain. The option -I is used to insert a policy rule before an existing policy line number (if used with no number, will insert at the top of the chain)
Examples:
| iptables -A INPUT -p tcp --sport 80 -j ACCEPT | Append policy to bottom of INPUT chain to accept all tcp packets from port 80 |
| iptables -A OUTPUT -p tcp --dport 80 -j ACCEPT | Append policy to bottom of OUTPUT chain to accept all tcp packets to port 80 |
| iptables -I INPUT -p tcp --sport 22 -j LOG | Insert policy at top of INPUT chain to log all tcp packets from port 22 |
| iptables -I INPUT 3 -p tcp --dport 22 -j LOG | Insert policy before line 3 of INPUT chain to log all tcp packets from port 22 |
You can also set exceptions to the default policy for specific IP Addresses by using the options -d IPADDR or -s IPADDR
| iptables -A INPUT -p tcp -s 192.168.0.0/24 -sport 22 -j ACCEPT | Append policy to bottom of INPUT chain to ACCEPT tcp packets from IP Address 192.168.0.0 from communication port 22 |
| iptables -A OUTPUT -p tcp -d 192.168.0.138/24 -dport 80 -j REJECT | Append policy to bottom of OUTPUT chain to REJECT tcp packets to IP Address 192.168.0.138 via communication port 80 |
Perform the following steps:
- Remain in your c7host VM for this section.
- Set the default policy for the INPUT chain to DROP by issuing the command:
iptables -P INPUT DROP - Now try on your own to change the default policies for the OUTPUT chain to DROP
- Issue the commmand
iptables -Lto verify that the policies on your INPUT and OUTPUT chain are set to DROP - Open a browser and attempt to access the Internet. Were you successful?
- Using the commands you have learned so far, change the policies on the INPUT and OUTPUT chains to ACCEPT
- Open your browser and attempt to access the Internet again. Were you successful?
- Change the policies on all of the chains to DROP
- In the OUTPUT chain, add the following rule:
iptables -A OUTPUT -j LOG. The above rule tells iptables to log packets and relevant information to /var/log/messages. - Try to access the Internet again. Because the policies have been set to DROP, you should be unsuccessful. However, every packet of data that your PC attempted to send out was logged.
- Let's have a look at the log file and analyze the data:
tail /var/log/messages
- This command shows us the last 10 lines of the file. While there are many things being logged to this file, the last thing we did was try to access the Internet so we should be able to see the data we need. Look for a line that looks similar to the following:
Jun 24 12:41:26 c7host kernel: IN= OUT=lo SRC=127.0.0.1 DST=127.0.0.1 LEN=52 TOS=0x00 PREC=0x00 TTL=64 ID=16442 DF PROTO=TCP SPT=57151 DPT=5902 WINDOW=1024 RES=0x00 ACK URGP=0
Your IP, host names and date will be different, but the one thing that should be the same is the DPT=80 value. When your computer tried to send OUT a request to connect to the Internet using the WWW, the computer used a destination port of 80. This is the standard port for the WWW. Because we have set the default policy to DROP it drops these packets. The problem is we are dropping all packets. What if we just want to drop the WWW packets?
- This command shows us the last 10 lines of the file. While there are many things being logged to this file, the last thing we did was try to access the Internet so we should be able to see the data we need. Look for a line that looks similar to the following:
- Using the commands we already know, change the default policies on all of your chains to ACCEPT.
- Open a browser and confirm that you can access the world wide web.
- Enter the command:
iptables -I OUTPUT -p tcp -s0/0 -d 0/0 --dport 80 -j DROP - Try to access the Web. If you have done everything right, you should not have been successful.
- After you have completed the test execute the following command:
iptables -F - Using the information you have learned, try on your own to achieve the same goal as above (block www access to your computer) by using the INPUT chain instead of the OUTPUT chain.
- After you have completed this task, flush the iptables again.
- Make sure that your ssh server is running on the host machine and try to access it from a virtual machine of your choice.
- Once you have confirmed that ssh is running on the host machine, insert an iptables rule on the host machine to prevent access to the ssh server from all VM's on the virtual network.
- Confirm that your rule works by testing from your VM's
- Does iptables close the port? Check using netstat
- Now insert a rule on the CentOS host that would ACCEPT connections from the centos3 VM only.
- Fully test your configuration.
Making iptables Policies Persistent
Any changes to your iptables policy rules will be lost when you restart your Linux server, unless you make your iptables rules persistent. Failure to perform the following steps after setting up your firewall rules can cause confusion and wasted time.
Perform the following steps:
- Make a backup of the file /etc/sysconfig/iptables by issuing the command:
iptables-save > /etc/sysconfig/iptables.bk - To make the iptables rules persistent (i.e. keeps rules when system restarts), you issue the command:
iptables-save > /etc/sysconfig/iptables - Verify that the file /etc/sysconfig/iptables exists.
- Restart your iptables service and test your configuration.
Answer INVESTIGATION 2 observations / questions in your lab log book.
LAB 6 SIGN-OFF (SHOW INSTRUCTOR)
Perform the Following Steps:
- Make certain that ALL of your VMs are running.
- Switch to your c7host VM.
- Change to the /root/bin directory.
- Issue the Linux command:
wget http://matrix.senecac.on.ca/~murray.saul/ops235/lab6-check.bash - Give the lab6-check.bash file execute permissions (for the file owner).
- Run the shell script and if any warnings, make fixes and re-run shell script until you receive "congratulations" message.
- Arrange proof of the following on the screen:
✓ centos2 VM:
✓c7host machine- ssh from centos2 to c7host VM.
✓ Lab6 log-book filled out.- A list of your iptables rules
- Output from running the network-info.bash shell script
- Run the lab6-check.bash script in front of your instructor (must have all
OKmessages)
Practice For Quizzes, Tests, Midterm & Final Exam
- What is a port?
- What command will set your IP configuration to 192.168.55.22/255.255.255.0 ?
- What file contains the systems
iptablesrules? - What is the difference between UDP and TCP?
- What port number is used for DHCP servers?
- What is the function of the file
/etc/services? - What is the function of the file
/etc/hosts? - What is the purpose of the file
/etc/sysconfig/network-scripts/ifcfg-eth0? - What tool is used to show you a list of current TCP connections?