OPS235 Lab 7
Contents
LAB PREPARATION
Purpose / Objectives of Lab 7
Setting up a computer network is very important, but there are many other operations that occur on a daily basis that can include trouble-shooting, repairing network connection issues as well as maintaining network security. System administrators need to protect or "harden" their computer networks from "penetration" from unauthorized computer users. Hardening a computer system can range from running an IDS (Intrusion Detection System) to monitoring and flagging suspicious activity to implementing screen savers on workstations.
In this lab, you will learn how to use ssh, scp, sftp commands to securely access and share data between authorized personnel. In addition, you will learn various methods of running and configuring an ssh server which include: using Public Key Authentication, setting up an SSH tunnel in order to securely run graphical applications safely among computers in the network, disabling root login, and changing the default ssh communication port to mislead potential penetration testers (also known as "pen-testers" or "hackers"). You will also learn how to setup a firewall using the iptables command in order to control the flow of packets throughout your computer server.
Main Objectives
- To set up, configure Secure Shell Services (ssh/sshd)
- To use the ssh, scp, and sftp clients to access, copy, or transfer data among Linux servers in a secure manner
- Use ssh to tunnel X applications
- To tunnel network traffic via other communication ports
- To customize sshd to create a more private, secure system
- Gain initial exposure to the iptables command used to configure and maintain a firewall for protection and troubleshooting
- Configure iptables to allow/disallow/forward different types of network traffic
| Minimum Required Materials |
Linux Command Reference | ||||
|
|
Networking Utilities ssh |
Additional Utilities hostname |
SSH Reference | ||
INVESTIGATION 1: INSTALLING AND MAINTAINING AN SSH SERVER
So far, you have learned to use the ssh utility to establish a secure connection to a remote server to perform tasks, administer the server. For these common operations, you have issued the ssh command, which is actually the client application for ssh. In order to connect to a remote server (like your VMs, Matrix, etc) they need to be running the SSH service (i.e. the ssh daemon).
In this section, you will learn how to install and configure an SSH server on an existing VM. You will also learn how to configure and use SSH in order to secure connections between your Linux machines (host as well as VMs).
Part 1: Confirming sshd service is Running on VMs.
- Perform the following steps:
- Launch your c7host machine and ALL of your VMs.
- Switch to your c7host VM.
- Create a file in your current directory with some text in it called: myfile.txt
- Issue the following command (using your Matrix login id):
scp myfile.txt yourmatrixid@matrix.senecac.on.ca:/home/yourmatrixidand enter your Matrix password. What did this command do? - Issue the following sngle command (using your Matrix login id):
ssh myfile.txt yourmatrixid@matrix.senecac.on.ca ls /home/yourmatrixidand enter your Matrix password.
What did this command do? How does it differ from using issuing the ssh command without the ls command? How is this useful?
The client ssh application contains the utlities: ssh, scp and sftp (learned in ULI101) to connect to remote Linux servers in order to issue commands or transfer files between Linux servers. You can install the SSH service on your Linux server, although this has already been performed upon installation. We will now confirm that the ssh service is running on all of your VMs. - OpenSSH should have been installed by default. Let's confirm this by issuing the command:
rpm -qa | grep ssh - You should see a number of packages installed including openssh-clients and openssh-server
-
openssh-serverinstalls a service called sshd. Confirm that this service is running by issuing the command:systemctl status sshd
- Now that you know the service is running, investigate what port number and protocol sshd uses by issuing the command:
netstat -atunp | grep sshd
What protocol and port is the sshd process using? What is the state of the port? Why would you think that UDP ports don't have a state? - Reissue the
netstatcommand without the -n option. What is the difference? - Make sure the sshd service is running on all 3 of your VM's
- Remember that you can view the /etc/services file in case you need to reference a service with a corresponding port number.
Part 2: SSH Server Security Configuration
Any time you configure your computer to allow logins from the network you are leaving yourself vulnerable to potential unauthorized access by so called "hackers". Running the sshd service is a fairly common practice but care must be taken to make things more difficult for those hackers that attempt to use "brute force" attacks to gain access to your system. Hackers use their knowledge of your system and many password guesses to gain access. They know which port is likely open to attack (TCP:22), the administrative account name (root), all they need to do is to "guess" the password.
Making your root password (and all other accounts!) both quite complex but easy to remember is not hard.
The Linux system administrator can also configure the SSH server to make the SSH server more secure. Examples include not permitting root login, and change the default port number for ssh.
- Perform the following steps:
- For this section, you will still be using your c7host and centos1 VMs.
- The next change you can make is to prevent the root account from logging in to sshd altogether.
- Change to your centos1 VM and open a terminal.
- Edit the file /etc/ssh/sshd_config and look for the option
PermitRootLogin. Un-comment the option (or add the option if it does not appear) and change the option value tono.
NOTE: Now any hacking attempt also has to guess an account name as well as the password. If you need to ssh with root access, ssh as a regular user and use su - to become root. - Even better, it is possible to restrict access to just specific users that require it:
Edit the file /etc/ssh/sshd_config and add a new option ofAllowUsers accountusing your login account for account - In order for these changes to take affect, you need to restart the sshd daemon. Issue the following command to restart the sshd service:
systemctl restart sshd - Try SSHing from your c7host VM to your centos1 VM as root. Where you successful? Now try SSHing from your c7host VM to your centos1 VM as a regular user that was permitted to connect via ssh. Did it work? What would happen for other user accounts that were not permitted?
- Finally, as a system administrator, you should periodically monitor your system logs for unauthorized login attempts.
- On CentOS systems the log file that is used is /var/log/secure
- It also logs all uses of the su and sudo commands.
- Attempt to connect to all of your VM's as root and other users using both public key and password authentication. Use some su and sudo commands also.
- Inspect the log to see what kind of information is logged.
Answer INVESTIGATION 1 observations / questions in your lab log book.
INVESTIGATION 2: ADDITIONAL METHODS TO SECURE YOUR SSH SERVER
Part 1: Generating Private and Public Keys (Public Key Infrastructure)
As a system administrator, you have the ability to generate or create public and private keys to ensure safe and secure ssh connections. This will require a user to prove who they say they are in order to access a Linux server via SSH (i.e. Authentication). The system administer can generate these keys for the first time, or if the system administrator suspects that a hacker has compromised or trying to penetrate the server, they can remove the existing keys and generate new keys.
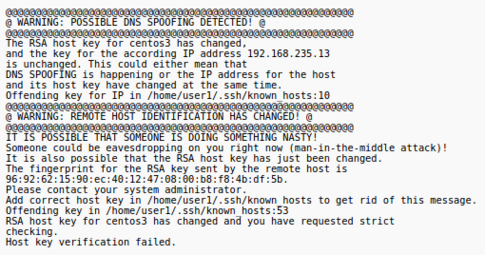
A common type of attack, Arp Poisoning (Man in the Middle Attack), can be used to redirect packets to a third party while maintaining the illusion that the connection is secure. Therefore, understanding about the generation and management of public/private keys are important to the security of servers.
- Perform the following steps:
- Switch to your centos3 VM.
- We can use the netstat utility as a trouble-shooting / confirmation tool to view the SSH service and determine which STATE the SSH service is performing: LISTENING, ESTABLISHED, CLOSED , or WAITING
- Run the netstat -atunp command (pipe to "grep sshd") to check the state of a possible ssh connection. What is the state (i.e. LISTENING or ESTABLISHED)?
- While in your centos3 VM, issue the following command to connect to the same VM via ssh:
ssh ops235@centos3 - Enter yes at the prompt, and enter your OPS235 password.
The output should appear similar as what is shown below:
- The authenticity of host 'centos3 (192.168.235.13)' can't be established.
- RSA key fingerprint is 53:b4:ad:c8:51:17:99:4b:c9:08:ac:c1:b6:05:71:9b.
- Are you sure you want to continue connecting (yes/no)? yes
- Warning: Permanently added 'centos3' (RSA) to the list of known hosts.
- The authenticity of host 'centos3 (192.168.235.13)' can't be established.
- Issue the following command to confirm that you connected to your centos3 VM:
hostname
- Re-run that same netstat pipeline command. Any change to the connection status?
- Log-out of your ssh connection by typing
exit. - Run that same netstat command again. Wait a few minutes and then check again. Record your observations.
So far, we have learned to establish an ssh connection to another host using a password to establish your identity. But passwords are not the only or even the best way of authenticating your identity. We can also use Public/Private key encryption.
Public Key authentication is a method of establishing identity using a pair of encryption keys that are designed to work together. One key is known as your private key (which as the name suggests should remain private and protected) and the other is known as the public key (which as the name suggests can be freely distributed) The keys are designed to work together to encrypt data asymmetrically, that is to say that when we encrypt data with one of the keys it can only be decrypted with the other key from the pair.
While it doesn't mean the message is secure as anybody could decrypt it with the public key, it does establish my identity, if the host can successfully decrypt the message then it must have come from the one person in possession of the private key.
- Switch to your centos2 VM.
- Confirm you are in your centos2 VM by entering the command:
hostname - Make certain that you are in your centos you are NOT logged in as root! (you have been warned!)
- To generate a keypair (public/private keys), issue the following command:
ssh-keygen - Press ENTER to accept the default, then enter a pass-phrase used to establish your identity, and re-enter the pass-phrase to verify.
The output should appear similar as what is shown below:
Generating public/private rsa key pair. Enter file in which to save the key (/home/ops235/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter passphrase again: Your public key has been saved in /home/ops235/.ssh/id_rsa.pub. The key fingerprint is: ef:de:31:67:f7:15:a4:43:39:15:5d:78:1b:e8:97:74 ops235@centos3 The key's randomart image is: +--[ RSA 2048]----+ | .+=| | .+oE| | .+.o=| | ..++ | | S o.. | | . . .| | . o o o| | . . = .o| | .o . .| +-----------------+
- After generating the keys it prompts you for the location to save the keys. The default is ~/.ssh Your private key will be saved as id_rsa and your public key will be saved as id_rsa.pub
- You will then be prompted for a pass-phrase. The pass-phrase must be entered in order to use your private key. Pass-phrases are more secure than passwords and should be lengthy, hard to guess and easy to remember. For example one pass-phrase that meets this criteria might be "seneca students like fish at 4:00am". Avoid famous phrases such as "to be or not to be" as they are easy to guess. It is possible to leave the pass-phrase blank but this is dangerous. It means that if a hacker were able to get into your account they could then use your private key to access other systems you use.
- Now issue the command
ssh-copy-id -i ~/.ssh/id_rsa.pub ops235@centos3 - When prompted for password, enter OPS235's root password
- Try using ssh to now log into your centos3 VM from your centos2 VM. What happens? Were you required to use your pass-phrase?
- Issue the hostname command to verify that you are successfully logged into your centos3 VM.
- Make certain to logout of your centos3 system. Use the hostname command to verify you are back in your centos2 server.
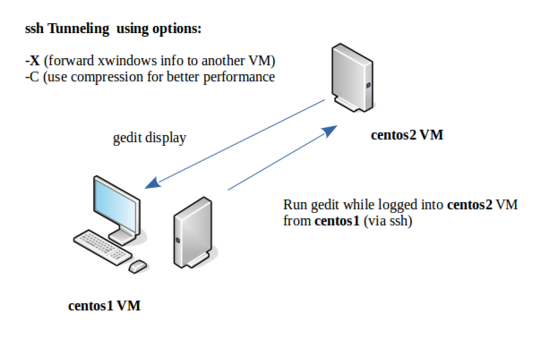
Part 2: Securely Running Graphical Applications Between Linux Servers
You can also use ssh to tunnel window and bitmap information, allowing us to login to a remote desktop host and run a Xwindows application such as gedit or firefox and the application will run on the remote host but be displayed on the local host.
- Perform the following steps:
- For this section, you will be using your c7host and centos1 VMs.
- Switch to your c7host VM, open a terminal and remain logged in as a regular user.
- Issue the following command to connect to your centos1 VM:
ssh -X -C yourUserID@centos1(where 'yourUserID' is your user account name on centos1)
(The -X option enables the forwarding of X window information, and the -C option enables compression for better performance). - Once the connection is properly established, run the command
gedit - The gedit window will display on your c7host VM, but in reality, this application is running on your centos1 VM!
- Enter some text and save your editing session.
- Exit the gedit application.
- In which VM was the file saved? What does that tell you about the use of tunneling for this section?
- Experiment with running other GUI applications through ssh.
Answer INVESTIGATION 2 observations / questions in your lab log book.
INVESTIGATION 3: MANAGING FIREWALLS FOR PROTECTION & TROUBLESHOOTING
Linux Firewall (iptables) Concepts
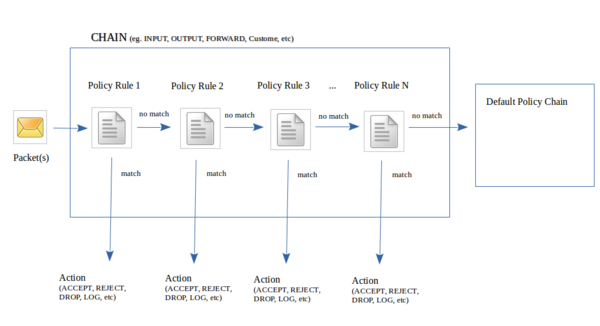
Since Linux servers can be connected to the Internet, it is very important to run a firewall to control what comes into the computer system, what goes out of the computer system, and what may be forwarded to another computer. A utility called iptables can be used to set the firewall rules on a Linux server.
Basically, there is a list (chain) of policy rules that packets must pass-through in order to handle packets. If a packet matches a rule, then an action is taken (some examples include: ACCEPT, DROP, REJECT, or LOG). If the packet passes through the chain of rules without a match, then the packet is directed to the default policy chain (for example: ACCEPT, REJECT, or DROP).
You can create your own customized chains (which you will learn in the OPS335 course) but to keep thing simple, we only deal with 3 common predefined chains:
- INPUT: Packets coming into current Linux server
- OUTPUT: Packets leaving current Linux server
- FORWARD: Packets being routed between Linux servers
Part 1: Listing & Clearing Existing iptables Rules
Let's get some practice using the iptables command as we introduce concepts such as listing CHAIN rules, and clearing the CHAIN rules:
- Perform the following steps:
- For the remainder of this section, use your c7host machine.
- Issue the following command to list the existing iptables policy rules:
iptables -L. - Were there already iptables policy rules that already existed by default?
- Before we proceed, we need to understand various methods to list iptables rules:
Listing iptables Rules:iptables -L List all iptables rules (eg. INPUT, OUTPUT. FORWARD, and any customized chains (if any) iptables -L -v Verbosely List all iptables rules including information such as total size of packets affected by rules iptables -L CHAIN-NAME List all iptables rules for that particular chain-name for less clutter (eg. INPUT or OUTPUT, etc) - Issue the following Linux command:
iptables -L INPUT
What do you notice is different with this command compared to the previous iptables command? - Issue the iptables command separately to display the rules for the OUTPUT chain and for the FORWARD chain.
- Issue the following command:
iptables -L -v
What do you notice about this command as opposed to the first iptables command you issued? What sort of additional information does this command provide regarding affected packets? - Sometimes it may be useful to completely clear the rules for all or a particular chain. Note the options that can be used to clear (or flush) the iptables rules,
Clearing (Flushing) iptables Rules:iptables -F Clears the rules for ALL of the chains iptables -F CHAIN-NAME Clears the rules for only the specified CHAIN-NAME (eg. INPUT or OUTPUT) - Issue the following command to reset the iptables rules for the INPUT chain:
iptables -F INPUT - Issue the iptables -L INPUT command to verify that the iptables rules for the INPUT chain have been cleared.
- Now, issue the command:
iptables -F
and then issue the command:iptables -L. What do you notice?
Part 2: Setting a Default Policy / Setting Policy Exceptions (iptables)
Usually when setting policy rules with iptables, a general "overall" policy is set (default policy chain). A good way to think about setting policies is to have a safety net to take some sort of action to prevent un-handled packets from passing through the firewall by mistake.After the default policy is set-up, then specific exceptions to the default policy can be added to control specific network traffic.
An example would be to set a default policy for incoming network traffic (INPUT chain) to DROP everything, and then set an exception certain exceptions (like ssh connections). Note the following table below for policy setting examples.
- Policy Setting Examples:
iptables -P INPUT DROP Drops all incoming packets regardless of protocol (eg. tcp, udp, icmp), port numbers (eg. 22, 80) or source or destination IP Addresses. Setting a default rule to DROP all incoming traffic would make it easier to specify a few exceptions. iptables -P INPUT ACCEPT Accepts all incoming packets regardless of protocol (eg. tcp, udp, icmp), port numbers (eg. 22, 80) or source or destination IP Addresses. It would seem that setting a default rule to ACCEPT all incoming traffic would require A LOT of exceptions to help "lock-down" the server for protection! It really depends on the server set-up and what the Linux system administrator wants to accomplish.
- Perform the following steps:
- Issue the following Linux command:
iptables -P INPUT DROP - Issue the iptables command verify the INPUT policy has been set (look for the Policy section, NOT INPUT).
After the overall default policy is set, then you can create policy rules that are "exceptions" to the default policy rules. These iptables commands are more complex since you need to determine:- Where each rules appears in the chain? (order can be important)
- Which protocol(s) are affected (eg. tcp, udp, icmp)
- What source or destination IP Addresses are affected?
- What port numbers are affected?
- What action to take if all of the above conditions are met? (eg. ACCEPT, REJECT, DROP, or LOG)
iptables Command Structure (for setting exceptions):
(NOTE: If element in column is not specified in the iptables command, then rule relates to ALL elements)Place Rule in Chain Chain Name Specify Protocol Source/Destination IPADDR Port Number Action
->Target -A (add / Append to bottom of chain)
-I (insert at top of chain)
-i CHAIN-NAME 5 (insert before line 5)INPUT
OUTPUT
FORWARD
CHAIN-NAME-p tcp (tcp packets)
-p udp (datagram packets)
-p tcp,udp,icmp (combined)
(refer to /etc/protocols )-s IPADDR (originating IPADDR)
-d IPADDR (destination IPADDR)--sport 22 (originating port 22 - SSH)
--sport 80 (originating port 80 - http)
(refer to /etc/services)-j ACCEPT
REJECT
DROP
LOG - Make certain you are in your c7host machine.
- Determine the external facing address of your c7host machine (ip address should start with 10. - otherwise, type ip address in web-browser)
- Have a lab neighbour try to ping that external facing address. Were they successful?
- Issue the following iptables policy to DROP all incoming connections:
iptables -P INPUT DROP - Have your neighbour try to ping your external facing IP Address. What happened? Why?
- Have your neighbour obtain the external facing IP Address on THEIR c7host machine.
- Issue iptables command to ADD ping exception from your neighbour's IPAddress
iptables -A INPUT -p icmp -s {neighbour's exeternal facing address} -j ACCEPT
Is your neighbour able to ping YOUR external facing IP Address? - Have your neighbour try to SSH into YOUR c7host. Were they Successful?
- Issue the following iptables command:
iptables -A INPUT -p tcp -s {neighbour's exeternal facing address} --sport 22 -j ACCEPT - Have your neighbour try to SSH into YOUR c7host. Were they Successful? If so, why?
- Issue the following iptables command to add a rule at bottom of OUTPUT chain to DROP http (port 80 connections). Try to think of the command yourself.
- Open another web-browser. Can you connect to a webpage?
- Issue iptables rule to flush the OUTPUT chain. Does your web-browser now work?
- Shutdown all VMs and restart your c7host Linux machine.
- List the iptables rules for the INPUT chain. What happened to your iptables rules for the INPUT chain?
- Proceed to the next part to learn how to learn how to make your iptables rules persistent.
Part 3: Making iptables Policies Persistent
Any changes to your iptables policy rules will be lost when you restart your Linux server, unless you make your iptables rules persistent. Failure to perform the following steps after setting up your firewall rules can cause confusion and wasted time.
- Perform the following steps:
- Flush all of your iptables rules by issuing the following command:
iptables -F - Verify there are no iptables rules by issuing the command:
iptables -L - Make a backup of the file /etc/sysconfig/iptables by issuing the command:
iptables-save > /etc/sysconfig/iptables.bk - To make the iptables rules persistent (i.e. keeps rules when system restarts), you issue the command:
iptables-save > /etc/sysconfig/iptables - Verify that the file /etc/sysconfig/iptables exists.
- Restart your iptables service and test your configuration.
Answer INVESTIGATION 3 observations / questions in your lab log book.
LAB 7 SIGN-OFF (SHOW INSTRUCTOR)
- Perform the Following Steps:
- Make certain ALL of your VMs are running.
- Switch to your c7host VM and su - into root.
- Change to the /root/bin directory.
- Issue the Linux command:
wget http://matrix.senecac.on.ca/~murray.saul/ops235/lab7-check.bash - Give the lab7-check.bash file execute permissions (for the file owner).
- Run the shell script and if any warnings, make fixes and re-run shell script until you receive "congratulations" message.
- Arrange proof of the following on the screen:
✓ centos2 VM:
✓ c7host Machine:- have logged into centos3 VM using public key authentication (with a pass-phrase)
✓ Lab7 log-book filled out.- have tunneled Xwindows application from centos1 via ssh
- Run the lab7-check.bash script in front of your instructor (must have all
OKmessages)
Practice For Quizzes, Tests, Midterm & Final Exam
- What port does sshd use by defaults?
- What file is used to configure sshd?
- What kind of files are stored in the "~/.ssh/" directory?
- How do you determine whether the sshd service is running on your system or not?
- What is the purpose of the ~/.ssh/known_hosts file?
- What is the purpose of the ~/.ssh/authorized_keys file?
- Which system log file records each use of the sudo command?
- How do you stop the sshd service?
- How do you tunnel XWindows applications?
- What port is the default ssh port?
- What port(s) is/are used by httpd service?