Difference between revisions of "OPS335 FTP Lab"
(Adding warning for known but in f16.) |
m (Adding new instruction for selinux) |
||
| Line 36: | Line 36: | ||
#*Enable file transfer logging. | #*Enable file transfer logging. | ||
#You'll now have to modify your vm01 firewall to allow NEW tcp connections on port 21. | #You'll now have to modify your vm01 firewall to allow NEW tcp connections on port 21. | ||
| − | #You'll | + | #You'll need to set SELinux to permissive mode: setenforce 0. |
| + | #You'll also need to tell SElinux to allow ftp access to users' home directories with: setsebool ftp_home_dir 1 | ||
| + | #*Note that this may take a minute to run. | ||
#Verify that the ftp connection tracking module is installed in your kernel with the "lsmod" command. If it is not, you'll have to install it with the command: "modprobe nf_conntrack_ftp". | #Verify that the ftp connection tracking module is installed in your kernel with the "lsmod" command. If it is not, you'll have to install it with the command: "modprobe nf_conntrack_ftp". | ||
#Start your ftp server. | #Start your ftp server. | ||
#At this point you should test your FTP server from hosts within your intranet. It should work properly for both anonymous and local users. From a terminal window on the gateway try these activities: | #At this point you should test your FTP server from hosts within your intranet. It should work properly for both anonymous and local users. From a terminal window on the gateway try these activities: | ||
| − | |||
#*ftp as anonymous to your VM, then list and get files. | #*ftp as anonymous to your VM, then list and get files. | ||
| + | #*ftp as your user name on your VM, then list, get and put files. | ||
===Configure the Firewall=== | ===Configure the Firewall=== | ||
Revision as of 17:36, 11 October 2012
Contents
VSFTP Setup
This lab will show you how to set up an FTP server inside a VM guest on a Fedora 16 host. Since you'll be using a VM as the FTP server, you'll only require one lab PC. Remember, these are not group labs - please work individually.
Background Information:
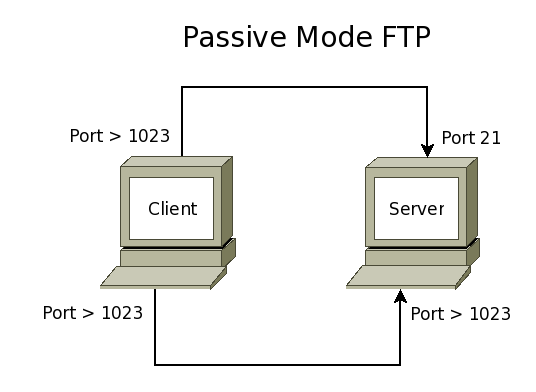
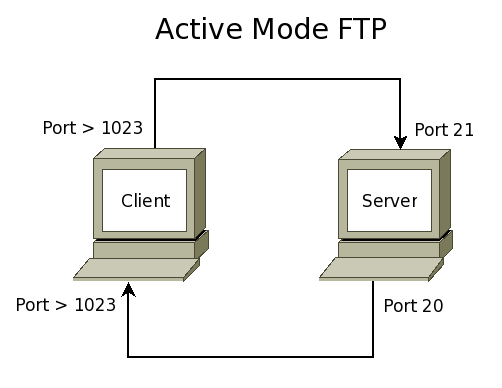
FTP uses 2 TCP ports. The first, usually port 21, is used to send commands to the server (ls, cd, get, put, etc.) and to receive command replies from the server. The second, usually port 20, is used to send a file to the server during an upload or to receive a file from the server during a download.
- FTP can work in 2 modes: Active or Passive.
- In active mode the client connects to the server on port 21. The server then connects back to the client from port 20. In both connections, the ports used on the client are insecure high-numbered ports ( greater than 1023 ).
- In passive mode the client first connects to the server on port 21 and makes a second connection to a high-numbered port. As with active mode, the ports used on the client are insecure high-numbered ports ( greater than 1023 ).
FTP can be set up so that anonymous users (users without accounts on the server) may download and possibly upload files.
Configure your VM
- Power up your PC (the gateway with host name f16), login as your user-id, open a terminal window and "su" to root.
- Check the settings on your firewall. Ensure that you can still use the services you have configured in previous labs.
- Check your firewall using the "iptables-save" command.
- Now make sure you are connected to the Internet. Start Firefox and authenticate yourself into the network.
- Still as root you need to install an ftp client. Use this command: "yum install ftp".
- Login to your VM01 and ensure you have the firewall set up to allow the services you have previously configured (e.g. DNS, mail). If those services are not functioning, fix them (or your firewall) now.
Before preceeding to the next part ensure your gateway is working properly and that your server has full access to the Internet. Try some of these commands on your VM guest:
ping 192.168.X.1 host cbc.ca
also use lynx from your vm to ensure you can view internal and external web sites.
Set up your FTP Server (Passive Mode)
- Still on vm01 use yum to install vsftpd and edit the config file (/etc/vsftpd/vsftpd.conf) to implement the following:
- Anonymous users should be able to login and download any files (permissions allowing) from the /var/ftp/pub.
- Anonymous uploading should not be allowed.
- Local users should be allowed to login to their own accounts and upload/download their own files.
- The FTP Greeting Banner should be set to "Welcome to OPS335 FTP Server".
- Set the maximum number of concurrent client connections to 50.
- Set the maximum transfer rate for anonymous users to 110912 bytes per second.
- Set the connection timeout for all clients to 90 seconds.
- Enable file transfer logging.
- You'll now have to modify your vm01 firewall to allow NEW tcp connections on port 21.
- You'll need to set SELinux to permissive mode: setenforce 0.
- You'll also need to tell SElinux to allow ftp access to users' home directories with: setsebool ftp_home_dir 1
- Note that this may take a minute to run.
- Verify that the ftp connection tracking module is installed in your kernel with the "lsmod" command. If it is not, you'll have to install it with the command: "modprobe nf_conntrack_ftp".
- Start your ftp server.
- At this point you should test your FTP server from hosts within your intranet. It should work properly for both anonymous and local users. From a terminal window on the gateway try these activities:
- ftp as anonymous to your VM, then list and get files.
- ftp as your user name on your VM, then list, get and put files.
Configure the Firewall
- Now configure your firewall (using iptables) on the gateway to allow FTP clients through to the vm01 FTP server.
- You'll need to forward packets with destination port 21 to your VM machine.
- Test your firewall by logging into a second PC (try both Windows and Linux) and attempt an FTP connection to your gateway PC. Test both local user as well as anonymous connections.
Set up your FTP Server (Active Mode)
- Edit /etc/vsftpd/vsftpd.conf and disable Passive mode (so now only Active mode is enabled) and then restart vsftpd.
- Test your firewall by logging into a second PC (try both Windows and Linux) and attempt an FTP connection to your gateway PC. Test both local user as well as anonymous connections.
Log Packets with Netfilter
- On the firewall/gateway add iptables log rules to monitor ftp traffic (control and data) for the following:
- PREROUTING chain of nat table
- FORWARD chain of filter table
- POSTROUTING chain of nat table
- On vm01 add iptables log rules to monitor ftp traffic (control and data) for the following:
- PREROUTING chain of nat table
- INPUT chain of filter table
- OUTPUT chain of filter table
- POSTROUTING chain of nat table
- While monitoring your packets using "tail -f /var/log/messages" - test your firewall by logging into a second PC (try both Windows and Linux) and attempt an FTP connection to your gateway PC. Test both local user as well as anonymous connections.
Completing the Lab
Answer the following questions and and email them to your teacher in ASCII text format.
- What is your full name and 9-digit Seneca student ID?
- Hand in your output from the following commands on the FTP server:
- cat /etc/vsftpd/vsftpd.conf | grep -v ^# | awk 'NF>0'
- cat /var/log/xferlog
- iptables-save
- Hand in your output from the following commands on the gateway:
- iptables-save
- Show the log files on both the gateway (f13) and the server (vm01) generated during while logging packets with Netfilter.