Difference between revisions of "OPS235 Lab 6 - Fedora17"
Chris Tyler (talk | contribs) (→Investigation 7: How can I see what network services or ports are active on my Fedora system?) |
Chris Tyler (talk | contribs) (→Investigation 8: How do I view and configure the IPTABLES firewall? -- Basic Function/Configuration) |
||
| Line 225: | Line 225: | ||
'''FORWARD''' – LINUX PC's are often used as routers or gateways for other PC's. This means that data may have to be passed through this LINUX box, but the data is not intended for the LINUX PC nor is it being sent by the LINUX PC. Even though the data will go into this PC and it will exit this PC, the INPUT and OUTPUT chains do not apply here. Because the PC is acting as a router it does not actually send or receive data, it FORWARDS data from one machine to another. When this process happens, the data is checked against the FORWARD chain to see if it is allowed through. If it is the router will forward the data to it's destination. If not, the packet is dropped.}} | '''FORWARD''' – LINUX PC's are often used as routers or gateways for other PC's. This means that data may have to be passed through this LINUX box, but the data is not intended for the LINUX PC nor is it being sent by the LINUX PC. Even though the data will go into this PC and it will exit this PC, the INPUT and OUTPUT chains do not apply here. Because the PC is acting as a router it does not actually send or receive data, it FORWARDS data from one machine to another. When this process happens, the data is checked against the FORWARD chain to see if it is allowed through. If it is the router will forward the data to it's destination. If not, the packet is dropped.}} | ||
| − | {{Admon/important | | + | {{Admon/important | Non-Persistent Changes to your Host System | Complete this lab on your host system (f13host). |
| − | It should be noted that all of the commands that we do here with iptables will not be persistent. | + | It should be noted that all of the commands that we do here with iptables will not be persistent unless you have your configuration. That means if you re-boot, the default iptables configuration will be loaded.}}1 |
| − | |||
| − | That means if you re-boot, the default iptables configuration will be loaded.}} | ||
| − | |||
# As root on the fedora host enter the following commands at the prompt: | # As root on the fedora host enter the following commands at the prompt: | ||
| Line 265: | Line 262: | ||
#* <code>iptables -I OUTPUT -p tcp -s0/0 -d 0/0 --dport 80 -j DROP</code> | #* <code>iptables -I OUTPUT -p tcp -s0/0 -d 0/0 --dport 80 -j DROP</code> | ||
| − | {{Admon/note| |This command can be read like this | + | {{Admon/note| Interpreting iptables commands |This command can be read like this: Insert a rule into the iptables OUTPUT chain that will match any tcp packet, with any a source address, any destination address, and a deistination port of 80. Any packet that matches will be dropped. |
| + | |||
| + | Let's break down the command to see how it works. | ||
| − | The '''-I''' switch tells iptables to INSERT this line into the OUTPUT policy. This means it will be the first line in the policy. If we used a -A switch it would have appended the line and it would be the last line of the policy. If you are writing complex iptables rules where multiple matches can occur, it is important that the lines go in the right order. | + | The '''-I''' switch tells iptables to INSERT this line into the OUTPUT policy. This means it will be the first line in the policy. If we used a -A switch it would have appended the line and it would be the last line of the policy. If you are writing complex iptables rules where multiple matches can occur, it is important that the lines go in the right order. If you follow the -I with a number, the new rule will be inserted at that location in the chain (for example, <code>-I 3 OUTPUT</code> will insert the rule into the 3rd position in the OUTPUT chain, moving the existing rules down as necessary (the old rule #3 will become the new rule #4, for example). |
| − | The '''-p tcp''' switch tells iptables to | + | The '''-p tcp''' switch tells iptables to only match TCP packets. Alternately, the protocol could be set to udp, icmp, or all. |
| − | The '''-s0/0''' switch specifies the source IP address. 0/0 means a source address of “anywhere.” this has been put into the lab because your ip address will change because it is dynamically assigned. You can change this value if you want to the IP address that has been specifically assigned to your PC. | + | The '''-s0/0''' switch specifies the source IP address. 0/0 means a source address of “anywhere.” this has been put into the lab because your ip address will change because it is dynamically assigned. You can change this value if you want to the IP address that has been specifically assigned to your PC. (Since the rule will, by default, match any source address, this switch may be left out). |
| − | The '''-d0/0''' switch specifies the destination address. It makes sense that this address is set to “anywhere” because if we want to block all requests to the WWW, we will never know the specific IP address of web server that is trying to be accessed. | + | The '''-d0/0''' switch specifies the destination address. It makes sense that this address is set to “anywhere” because if we want to block all requests to the WWW, we will never know the specific IP address of web server that is trying to be accessed. (Since the rule will, by default, match any destination address, this switch may be left out). |
| − | The switch '''--dport 80''' tells iptables to look at the destination port in the packet and see if it is equal to 80 | + | The switch '''--dport 80''' tells iptables to look at the destination port in the packet and see if it is equal to 80. Alternately, you can filter based on source addresses using the <code>--sport</code> switch. |
| − | '''-j''' means jump to a particular | + | '''-j''' means jump to a particular target – Basic targets are ACCEPT, DROP, REJECT, and LOG. The available targets depend on which table contains the chain. |
| − | '''DROP''' means drop the packet – do not | + | '''DROP''' means drop the packet – make it dissapear - and do not continue processing rules. '''REJECT''' is similar, but causes an error packet to be sent back to the source host. '''ACCEPT''' causes the packet to be processed. '''LOG''' causes an entry to be made in the system logs showing that the packet was processed. Note that the ACCEPT target is the only one that does not stop rule-checking in the chaing - so you can log a packet with one rule, and then use a later rule in the chain to DROP, REJECT, or ACCEPT it. |
}} | }} | ||
| Line 301: | Line 300: | ||
# Make a backup of the file <code>/etc/sysconfig/iptables</code> | # Make a backup of the file <code>/etc/sysconfig/iptables</code> | ||
# Examine the file to see how rules are added. | # Examine the file to see how rules are added. | ||
| − | # | + | # Issue the command: <code>service iptables save</code> to save the rules you added with the iptables command, above. |
| + | # Verify that the file <code>/etc/sysconfig/iptables</code> was updated with your new rules. | ||
| − | {{Admon/important | Carefull! | Remember mistakes in iptables can have a significant impact on your system. | + | {{Admon/important | Carefull! | Remember that mistakes in iptables can have a significant impact on your system.}} |
# Restart your iptables service and test your configuration. | # Restart your iptables service and test your configuration. | ||
| − | # Write a short bash script to | + | # Write a short bash script to add a rule allowing the fedora1 and fedora3 VM's to connect to <code>ssh</code> on the fedora host. |
| − | # Answer the investigation in your logbook | + | # Answer the investigation in your logbook. |
== New Configuration == | == New Configuration == | ||
Revision as of 19:41, 13 March 2011
Contents
- 1 Configuring a Network Using Virtual Machines
- 1.1 Objectives
- 1.2 Reference
- 1.3 Required materials
- 1.4 Current Configuration
- 1.5 Lab Preparation
- 1.6 Lab Investigations
- 1.6.1 Investigation 1: How do you create a new virtual network.
- 1.6.2 Investigation 2: How do you configure a static network using system-config-network.
- 1.6.3 Investigation 3: What files does the system-config-network GUI tool change?.
- 1.6.4 Investigation 4: How do I configure the network without a GUI tool?.
- 1.6.5 Investigation 5: How do I setup local hostname resolution?
- 1.6.6 Investigation 6: How do I collect the MAC (Hardware) addresses of computers on my network?
- 1.6.7 Investigation 7: How can I see what network services or ports are active on my Fedora system?
- 1.6.8 Investigation 8: How do I view and configure the IPTABLES firewall? -- Basic Function/Configuration
- 1.7 New Configuration
- 1.8 Completing the lab
- 1.9 Preparing for the Quizzes
Configuring a Network Using Virtual Machines
Objectives
- Configure a virtual network for Virtual Machines
- Use the Fedora GUI program to configure network interfaces with static IP configuration and host name resolution
- Use the
findcommand to locate the configuration files modified by the GUI network configuration program
- To examine some of the Linux's TCP/IP configuration files in the
/etc/directory - To configure a Fedora host with static network configuration without a GUI tool
- To use and interpret the
netstatcommand to troubleshoot and monitor network services
- To configure the linux firewall
iptablesto allow/disallow/forward different types of network traffic using simple rules
Reference
- man pages for find, ifconfig, ping, netstat, NetworkManager, nslookup, iptables, arp
- Online reading material for week 8.
Required materials
- Your SATA hard disk in a removable drive tray with Fedora host and 3 Fedora Virtual Machines installed
Current Configuration
Currently you should have the following network configuration:
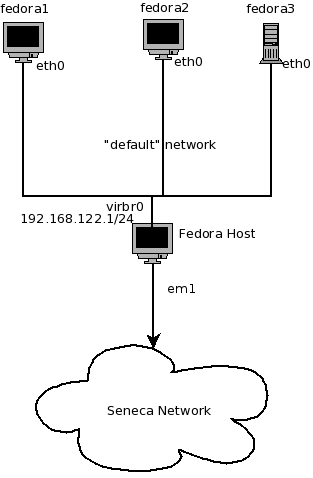
- Fedora host has 1 active network interface (probably
eth0)that receives IP configuration from the School's DHCP server. - Fedora host has 1 active network interface (
virbr0) that has a static default configuration of 192.168.122.1/255.255.255.0 - Fedora1 VM has 1 active interface (
eth0) that receives a dynamic configuration from your Fedora Host - Fedora2 VM has 1 active interface (
eth0) that receives a dynamic configuration from your Fedora Host - Fedora3 VM has 1 active interface (
eth0) that receives a dynamic configuration from your Fedora Host
Lab Preparation
Lab Investigations
Investigation 1: How do you create a new virtual network.
Before configuring our network we want to turn off dynamic network configuration for our Virtual Machines by turning off the "default" virtual network.
- On the fedora host start Virtual Machine Manager
- In the Virtual Machine Manager dialog box, Select Edit-> Connection Details.
- In the Hosts Details dialog box, select the Virtual Networks tab
- Disable the default configuration from starting at boot by deselecting the "Autostart On Boot" checkbox.
- Stop the default network configuration by clicking on the stop button at the bottom of the window.
- Click on the add button (plus sign) to add a new network configuration.
- Give your new network a name (network1)
- Enter in the new network IP address space:
- 192.168.235.0/24
- Disable DHCP by deselecting the check box.
- Enable Network Forwarding by Selecting "Forwarding to physical network"
- The destination should be "Any physical device" and the mode should be "NAT"
- Proceed with changes, and select Finish.
- Before proceeding, check the "default" network connection (in the Virtual Networks section) to verify "Autostart On Boot" is disabled, and that you have created the "network1" configuration. If you have any problems launching your VMs, then it is recommend to reboot your main system.
- Now we need to add our new virtual network "network1" to the 3 VM's
- Select the fedora1 VM and edit the VM details
- Under View select Details
- In the left pane select the NIC and note that this NIC is on the "default" virtual network
- Click on the Remove button
- Click on "Add Hardware" and add a new network
- For the host device select "Virtual Network network1" : NAT
- Repeat these steps for fedora2 and fedora3 VM's
- Answer the Investigation 1 question in your lab log book.
Investigation 2: How do you configure a static network using system-config-network.
- Start fedora2 VM and login
- On your fedora host run
ifconfigand make note of the IP address assigned to thevirbr1interface. This will be your default gateway for your Vm's. - To configure a new interface on fedora2 go to System->Administration->Network and click on the "New" button
- Select Ethernet Device and choose the network card named
eth1 - Statically set the IP configuration:
- IP Address 192.168.235.12
- Subnet Mask 255.255.255.0
- Default Gateway 192.168.235.1 (The IP address of
virbr1on your fedora host.)
- Click on the DNS tab and add 192.168.235.1 as the primary DNS server.
- Select Forward, and then select Apply to Finish.
- Restart your network on fedora2.
service NetworkManager restart - Verify your new interface by examining the output of
ifconfig - To verify that fedora2 has the correct default gateway configured, enter the command
route -n - Verify the network by using
ping 192.168.235.1 - Record the answer to Investigation 2 in your logbook.
Investigation 3: What files does the system-config-network GUI tool change?.
- Start fedora1 VM and login
- Before we configure fedora1 we should create a timestamp file that can be used to see which files have changed as a result of using the GUI tool.
-
date > /tmp/timestamp
-
- Run the network configuration tool and enter the following static configuration in the same way that you configured fedora2.
- IP Address: 192.168.235.11
- Subnetmask: 255.255.255.0
- Default Gateway: 192.168.235.1
- DNS Server: 192.168.235.1
- Save and quit and restart NetworkManager
- Verify the configuration by pinging fedora host (192.168.235.1) and fedora2 (192.168.235.12)
- To verify that fedora1 has the correct default gateway configured, enter the command
route -n - Use the
findcommand to locate the configuration files modified by the GUI network configuration program- Previously, you created a file called
/tmp/timestamp. Any files that were modified by the GUI network configuration program should have a timestamp later (or newer) than the "timestamp" file you created. All the Linux TCP/IP configuration files are stored under the "/etc" directory or its sub-directories. The following command when run as root will give you a list of all the files under the/etcdirectory with a file modification date newer than the date of the "timestamp" file:find /etc -newer /tmp/timestamp
- Previously, you created a file called
- Capture the output to a file called
netcfg.lstunder user root's home directory. - Create a new directory called
/tmp/lab6and copy all the files from thefindcommand to it.- There are a number of ways to accomplish this:
- Edit
netcfg.lstand turn it into a bash script. - Copy the files manually using the
cpcommand. - Investigate the
-execoption of thefindcommand to see how to find and copy the files with a single command.
- Edit
- There are a number of ways to accomplish this:
- Record the answer to the investigation in your lab log.
Investigation 4: How do I configure the network without a GUI tool?.
- Start fedora3 VM and login as root
- Use the command
ifconfigto list active interfaces, you should see one with a name ofeth1or a similar name. - To configure your card with a static address use the command:
-
ifconfig eth1 192.168.235.13 netmask 255.255.255.0
-
- To configure a default gateway for that interface enter the command:
-
route add default gw 192.168.235.1
-
- To configure your DNS server edit the file
/etc/resolv.conf. Change thenameserverline to be:-
nameserver 192.168.235.1
-
- Confirm your settings work by doing the following:
-
ifconfig -
route -n -
pingyour other VM's and fedora host. -
sshto your matrix account to test DNS
-
- Restart the
fedora3VM - Login and test your configuration again. What happened?
- While we can configure network settings from the command line those settings are not persistent. To configure persistent network configurations we need to edit the configuration files:
- Change to the
/etc/sysconfig/network-scriptsdirectory onfedora3 - List the contents of the directory and you should see 2 different types of files, network config scripts and network configuration files.
- look for the config file for your original interface, it should be named
ifcfg-eth0 - Copy that file to
ifcfg-eth1or whatever name matches your current eth interface. - Edit the new file for you interface and give it the following settings:
- GATEWAY=192.168.235.1
- DNS1=192.168.235.1
- DEVICE=eth1 <-- or the interface name you have
- BOOTPROTO=none
- NETMASK=255.255.255.0
- TYPE=Ethernet
- HWADDR=52:54:00:3f:5c:fa <--use the HWADDR for your interface
- IPADDR=192.168.235.13
- IPV6INIT=no
- ONBOOT=yes
- USERCTL=no
- Change to the
- Save the file and restart the
NetworkManagerservice - Verify your configuration as you did before.
- Finally the kickstart file used to install this VM did not set the hostname. Edit the file
/etc/sysconfig/networkand set the hostname tofedora3 - Restart the
fedora3VM. - Login and attempt to
sshto your matrix account to verify the settings. - Answer the Investigation question in your logbook.
Investigation 5: How do I setup local hostname resolution?
- Use the
hostnameandifconfigcommands on your fedora host and all 3 VM's to gather the information needed to configure the/etc/hostsfile on the fedora host and the 3 VM's. - Edit the
/etc/hostsfile on each of the virtual machines and the fedora host. Confirm that each host can ping all three of the other hosts by name. - Answer the investigation in your logbook.
| Sample /etc/hosts file |
|---|
# hostname fedora1 added to /etc/hosts by anaconda 127.0.0.1 localhost.localdomain localhost fedora1 ::1 localhost6.localdomain6 localhost6 fedora1 192.168.235.1 f13host 192.168.235.11 fedora1 192.168.235.12 fedora2 192.168.235.13 fedora3 |
Investigation 6: How do I collect the MAC (Hardware) addresses of computers on my network?
While we use 32bit IP addresses to communicate over an internetwork, on the local ethernet network packets are delivered to a 48bit hardware address (sometimes called a MAC address). The ARP protocol resolves 32bit IP addresses to 48bit MAC addresses by using a broadcast and caching the results. We can examine the ARP cache to get the MAC addresses of other computers on our local network.
- On the fedora host
pingeach of your VM's - Examine the contents of the ARP cache by using the command
arp - Check the contents of the cache again by using the command
arp -n - What was the difference in output?
- Answer the investigation question in your logbook
Investigation 7: How can I see what network services or ports are active on my Fedora system?
- On your fedora host execute the command
netstat -at - This command will list all active TCP ports. Note the state of your ports.
- TCP is a connection oriented protocol that uses a handshaking mechanism to establish a connection. Those ports that show a state of LISTEN are waiting for connection requests to a particular service. For example you should see the
sshservice in a LISTEN state as it is waiting for connections. - From one of your VM's login to your host using
ssh - On the fedora host rerun the command and in addition to the LISTEN port it should list a 2nd entry with a state of ESTABLISHED. This shows that there is a current connection to your ssh server.
- Exit your ssh connection from the VM and rerun the command on the fedora host. Instead of ESTABLISHED it should now show a state of CLOSE_WAIT. Indicating that the TCP connection is being closed.
- On your fedora host try the command
netstat -atn. How is this output different? - Without the
-noptionnetstatattempts to resolve IP addresses to host names (using /etc/hosts) and port numbers to service names (using /etc/services) - Examine the
/etc/servicesfile and find which ports are used for the servicesssh ftp http - Now execute the command
netstat -auWhat is the difference between-atand-au? - When examining UDP ports why is there no state?
- Using the
netstatman page and experimentation make sure you understand how the following options work.- -at
- -au
- -atp
- -aup
- -atn
- -aun
- -autnp
- Answer the investigation your logbook
Investigation 8: How do I view and configure the IPTABLES firewall? -- Basic Function/Configuration
1- As root on the fedora host enter the following commands at the prompt:
-
iptables -F(This flushes out or clears all of your rules from the chains) -
iptables -L
-
- You should see something similar to this:
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
- Set the default policy for the INPUT chain to DROP:
-
iptables -P INPUT DROP
-
- Now try on your own to change the default policies for the OUPUT and FORWARD chains to DROP
- Write the commands you executed in your lab book.
- Can we mix these policies? Try to set the FORWARD chain policy to ACCEPT. Did it work?
Testing policies
- Execute the command
iptables -Land check that the policies on your INPUT and OUTPUT chain are set to DROP - Open a browser and attempt to access the Internet. Were you successful?
- Using the commands you have learned so far, change the policies on the INPUT and OUTPUT chains to ACCEPT
- Open your browser and attempt to access the Internet again. Were you successful?
- Change the policies on all of the chains to DROP
- In the OUTPUT chain, add the following rule:
-
iptables -A OUTPUT -j LOG
-
- The above rule tells
iptablesto log packets and relevant information to/var/log/messages. - This entry in the OUTPUT policy will therefore log all packets being sent out of the machine.
- Try to access the Internet again. Because the policies have been set to DROP, you should be unsuccessful. However, every packet of data that your PC attempted to send out was logged. Let's have a look at the log file and analyze the data.
-
tail /var/log/messages
-
- This command shows us the last 10 lines of the file. While there are many things being logged to this file, the last thing we did was try to access the Internet so we should be able to see the data we need. Look for a line that looks similar to the following:
Mar 3 09:21:03 koala-laptop kernel: [90775.407304] IN= OUT=wlan0 SRC=192.168.1.107 DST=66.249.90.104 LEN=1470 TOS=0x00 PREC=0x00 TTL=64 ID=19752 DF PROTO=TCP SPT=45431 DPT=80 WINDOW=108 RES=0x00 ACK PSH URGP=0 - Your IP, host names and date will be different, but the one thing that should be the same is the DPT=80 value.
- When your computer tried to send OUT a request to connect to the Internet using the WWW, the computer used a destination port of 80. This is the standard port for the WWW. Because we have set the default policy to DROP it drops these packets. The problem is we are dropping all packets. What if we just want to drop the WWW packets?
- Using the commands we already know, change the default policies on all of your chains to ACCEPT.
- Open a browser and confirm that you can access the world wide web.
- Enter the command:
-
iptables -I OUTPUT -p tcp -s0/0 -d 0/0 --dport 80 -j DROP
-
- Try to access the Web. If you have done everything right, you should not have been successful.
- After you have completed the test execute the following command:
-
iptables -F
-
Additional Exercises
- Using the information you have learned, try on your own to achieve the same goal as above (block www access to your computer) by using the INPUT chain instead of the OUTPUT chain.
- After you have completed this task, flush the iptables again.
- Make sure that your ssh server is running on the host machine and try to access it from a virtual machine of your choice.
- Once you have confirmed that ssh is running on the host machine, insert an iptables rule on the host machine to prevent access to the ssh server from all VM's on the virtual network.
- Confirm that your rule works by testing from your VM's
- Does iptables close the port? Check using
netstat - Now insert a rule on the fedora host that would ACCEPT connections from the fedora2 VM only.
- Fully test your configuration.
- Make a backup of the file
/etc/sysconfig/iptables - Examine the file to see how rules are added.
- Issue the command:
service iptables saveto save the rules you added with the iptables command, above. - Verify that the file
/etc/sysconfig/iptableswas updated with your new rules.
- Restart your iptables service and test your configuration.
- Write a short bash script to add a rule allowing the fedora1 and fedora3 VM's to connect to
sshon the fedora host. - Answer the investigation in your logbook.
New Configuration
Now you should have the following network configuration:
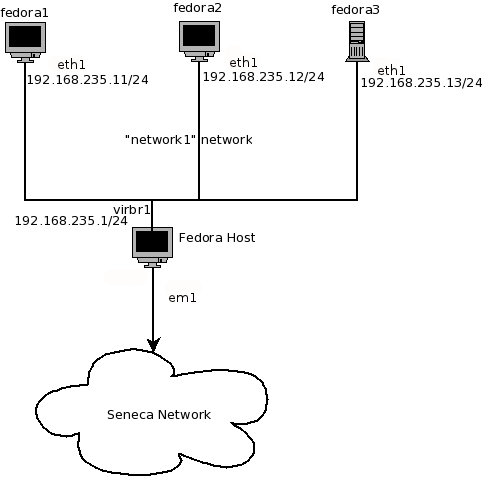
- Fedora host has 1 active network interface (probably
eth0)that receives IP configuration from the School's DHCP server. - Fedora host has 1 active network interface (
virbr1) that has a static default configuration of 192.168.235.1/255.255.255.0 - Fedora1 VM has 1 active interface (
eth1) that has a static configuration of 192.168.235.11/255.255.255.0 - Fedora2 VM has 1 active interface (
eth1) that has a static configuration of 192.168.235.12/255.255.255.0 - Fedora3 VM has 1 active interface (
eth1) that has a static configuration of 192.168.235.13/255.255.255.0
Completing the lab
Arrange proof of the following on the screen:
- A list of your
iptablesrules. - The contents of your
arpcache. -
sshfrom fedora2 to fedora host. -
ifconfigfrom all 3 VM's - Contents of
/tmp/lab6directory. - Fresh backup of the virtual machines.
- Run your bash script to allow VM's to access
sshon your fedora host.
Preparing for the Quizzes
- What is a port?
- What command will set your IP configuration to 192.168.55.22/255.255.255.0 ?
- What file contains the systems
iptablesrules? - What is the difference between UDP and TCP?
- What port number is used for DHCP servers?
- What is the function of the file
/etc/services? - What is the function of the file
/etc/hosts? - What is the purpose of the file
/etc/sysconfig/network-scripts/ifcfg-eth0? - What tool is used to show you a list of current TCP connections?