Difference between revisions of "OPS245 Lab 4"
m (Moving lab check link) |
Ahadalioglu (talk | contribs) (→Part 2: Adding, Removing, and Modifying Users) |
||
| Line 124: | Line 124: | ||
# Be sure to record your observations in your lab notes. | # Be sure to record your observations in your lab notes. | ||
#Issue the man pages for the '''useradd''' command. Explain the purpose of using the '''-e''' option for the ''useradd'' command. | #Issue the man pages for the '''useradd''' command. Explain the purpose of using the '''-e''' option for the ''useradd'' command. | ||
| − | #Issue the following command: <b><code><span style="color:#3366CC;font-size:1.2em;">sudo chage -E | + | #Issue the following command: <b><code><span style="color:#3366CC;font-size:1.2em;">sudo chage -E 2021-12-31 ops245_1</span></code></b> |
#Issue the following command: <b><code><span style="color:#3366CC;font-size:1.2em;">sudo usermod -c "New Name" ops245_2</span></code></b>. | #Issue the following command: <b><code><span style="color:#3366CC;font-size:1.2em;">sudo usermod -c "New Name" ops245_2</span></code></b>. | ||
#View ops245_2's account information in the '''/etc/passwd''' file. What do you notice is different? | #View ops245_2's account information in the '''/etc/passwd''' file. What do you notice is different? | ||
Revision as of 21:05, 10 January 2021
Contents
- 1 LAB PREPARATION
- 2 INVESTIGATION 1: User/Group Management
- 3 INVESTIGATION 2: Controlling Sudo Elevated Privileges
- 4 INVESTIGATION 3: Managing System Services and Run-levels
- 5 INVESTIGATION 4: CREATING USERS VIA SHELL SCRIPTS
- 6 LAB 4 SIGN-OFF (SHOW INSTRUCTOR)
- 7 Practice For Quizzes, Tests, Midterm & Final Exam
LAB PREPARATION
Purpose / Objectives of Lab 4
There are many other tasks that a Linux system administrator must perform other than installing Linux and installing software.
User account management is a very important operation that a Linux sysadmin does on an continual basis. The sysadmin not only needs to add or remove user accounts by issuing commands, but may need to automate user account creations a large number (batch) of potential employees. There are many features with the Linux command to create new users including: specification of a home directory, type of shell used, name, password and time-limit (referred to as "aging") for a new user account. Removing user accounts also have options such as removing the user account but keeping the home directory for reference or evidence of "wrong-doing"
Another important operation for a Linux sysadmin is to manage services (eg. starting, restarting, stopping, disabling, enabling system services). Many students may think that the following topic is small and "not a big deal". Those students may say, "How hard is running and stopping services?"
The process may not be hard, but knowing how to stop, start, restart and check the status of services is absolutely critical to a Linux server. Aside from learning to trouble-shoot problems by checking the status of running services, understanding how to manage services is critical to help protect a Linux server from penetration (this term is referred to as "Hardening a system"). Sometimes it is "what we don't know" that can harm us. One key element in hardening a computer system is to disable non essential networkng services to allow IDSs (Intrusion Detection Systems) to focus on a narrower range of policy violations. A Debian-based penetration testing distribution called Kali (formerly referred to as "BackTrax") allows sysadmins and security professionals to identify vulnerabilities in their computer systems, and thus improve (harden) their systems against penetration. Learning to monitor the status, enable and disable networking services underlies the Backtrax motto: "The quieter you are, then more you will hear..."
Main Objectives:
- Administer (add, remove, modify) users on a Linux system.
- Save time while adding new users using a template of start-up files.
- Create and manage groups on a Linux system.
- Start, Restart and Stop services on a Linux system.
- Enabled and Disable services on a Linux system.
- Display the status of running services on a Linux system.
- Create a Bash shell script to generate multiple user accounts from a text user database file
| Minimum Required Materials |
Linux Command Reference | ||||
| User Management
useradd |
Miscellaneous
/etc/passwd | ||||
INVESTIGATION 1: User/Group Management
In your ULI101 course, you learned to change permissions for directories and files relating to user, same group members and other group members. In this course, since you are the sysadmin with root privileges, you can create or remove users and groups as well as change the ownership of directories and files! We will now learn to perform key user account management operations in this section.
Part 1: Studying the /etc/passwd file
The /etc/passwd file is a database that stores user accounts (both system and regular users). Since we will be learning to create, modify and remove users on our Linux system, we should study this file in order to understand how those user account management commands will affect this file.
- Perform the following steps:
- Launch your c7host and centos1 VMs.
- Switch to your centos1 VM.
- Open a shell terminal.
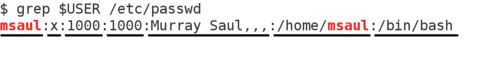
- Look at the
/etc/passwdfile. - Make note of the contents of that file.
- Read about the file: http://man7.org/linux/man-pages/man5/passwd.5.html
- Make sure you know what information each field contains.
- Why do you think there are so many users?
- Look at the names of the users. What do you think these user names represent? Are they people?
- What is the numeric user ID (UID) of the root user?
- The user IDs of real users (people) are different from the user IDs of system accounts. What is the pattern?
Part 2: Adding, Removing, and Modifying Users
In this section, we will now learn how to properly add user accounts, remove user accounts, and modify existing user account information.
- Perform the following steps:
- Remain in your centos1 VM for this section.
- Read the man page for the
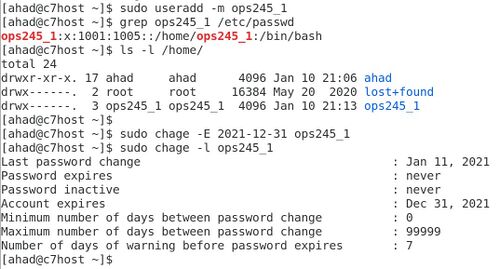
useraddcommand. - Create a new user called ops245_1 by issuing the command:
sudo useradd ops245_1 - Issue the command:
grep ops245_1 /etc/passwdto see if that user account was created. - View the /home directory to view the contents. Is the user ops245_1's home directory there?
NOTE: In some versions of Linux, you may have to issue the -m option with the useradd command in order to create a home directory for that user. - Issue the following command to create the user called ops245_2:
sudo useradd -m ops245_2 - View the /home directory to verify that the home directory for ops245_2 has been created. What does the -m option do for the useradd command?
- Issue the following command to remove the user called ops245_2:
sudo userdel ops245_2 - Issue the grep command with the /etc/passwd file to verify that the username ops245_2 was removed.
- View the contents of the /home directory. Was the home directory for user ops245_2 removed?
- Issue the following command to remove ops245_2's home directory:
sudo rm -rf /home/ops245_2 - Issue the userdel comamnd to remove the ops245_1 account with the -r option (and home directory regardless if it exists or not).
- Issue the useradd -m command to recreate the user called: ops245_1.
- Use the passwd command to set the password for the user ops245_1.
- View the contents for ops245_1's home directory and note the files.
- Create a new file in the /etc/skel directory with the following command:
sudo touch /etc/skel/foo - Recreate the new user (with home directories automatically created) for ops245_2.
- Set the password for the user ops245_2.
- View the contents for ops245_2's home directory and note the files. What do you notice that is different. What do you think is the purpose of the /etc/skel directory?
- Be sure to record your observations in your lab notes.
- Issue the man pages for the useradd command. Explain the purpose of using the -e option for the useradd command.
- Issue the following command:
sudo chage -E 2021-12-31 ops245_1 - Issue the following command:
sudo usermod -c "New Name" ops245_2. - View ops245_2's account information in the /etc/passwd file. What do you notice is different?
- Issue the following command to obtain information regarding the user called ops245_1:
sudo chage -l ops245_1. What do you think is the purpose of the chage command and the useradd command with the -e option?
Part 3: Managing Groups
In this section, we will learn how to create, remove and modify groups in our Linux VM. You learned in ULI101 how to change permissions with the chmod command, but you didn't have admin privileges to create groups to allow directory and regular file sharing. Since you now have admin privileges with your VM, you can now create groups, and add users to this group to allow file-sharing among users.
- Perform the following steps:
- Make certain that you are still in your centos1 VM.
- Close all application windows, and switch user accounts (within your centos1 VM) by clicking on the top right-hand side of the screen (power icon), click your regular username, click switch user, and login as "New Name" (i.e. ops245_2).
- Open a shell terminal.
- Create a file called information.txt in home directory of that user.
- Issue the following command:
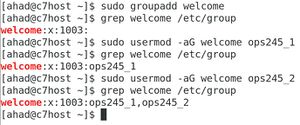
ls -l information.txt. Who owns that file? What primary group does that file belong to? - Issue the following command to create a group called welcome:
sudo groupadd welcome - You'll notice that sudo does not work for this user, because we haven't given them permissions to run any commands with elevated privileges.
- Log out, and log back in as your normal user.
- Now re-issue the command to create welcome group. This time, sudo should work.
- Issue the command:
grep welcome /etc/groupfile to confirm that the group welcome was created. - Read the man page for the
usermodcommand. Which option allow you to set the Group ID number (GID) when you create a new group? Which options allow you to both append and assign users to an existing group name? - Issue two separate usermod commands to add both ops245_1 and ops245_2 to the newly-created welcome group.
- Verify that both ops245_1 and ops245_2 now belong to the welcome group.
Practical Example
Management has sent you (the Linux systadmin) that a "new" employee has been hired and will be on on probation for 3 months. As the Linux system administrator, they want you to perform the following steps:
- Remain in your centos1 VM for this section.
- Use the useradd command to create a user account called: noobie to expire in 3 months from this date as part of the security policy of this organization (issue man useradd to determine correct option to set expiry date).
- Set an appropriate password for this user account.
- Add this newly-created user to the newly-created welcome group.
- Examine
/etc/groupto verify that you made the correct operations. - Use the usermod command to set the full name of the user account noobie to "Really Green". Examine the result of running that command in the
/etc/passwdfile. What has changed?
Unfortunately, you were later informed that this "noobie" employee was caught stealing from the company. They want you to perform the following operations: - Remove this account, but keep "noobie's" home directory for police investigation purposes.
- Verify that you correctly issued the correct commands.
Answer INVESTIGATION 1 observations / questions in your lab log book.
INVESTIGATION 2: Controlling Sudo Elevated Privileges
When you created your first user on your host, centos1 and centos2, you made them an administrator. This allowed them to (when they request it) run commands with root priveleges. But you won't always know in advance if a user is going to be an administrator (what if someone gets promoted, or changes jobs?), so you can't always do that in advance. Checking that box also allows them to run any command with root priveleges by using sudo. In many cases, administrators won't be allowed to do everything, but instead be restricted to certain tasks (e.g. managing user accounts, managing software, managing services, etc.). Sudo will allow us this detailed control, so we can pick and choose who gets to run which commands as root.
Part 1: Finding out why Your First User can do Anything?
You've already observed that your first user can use sudo to execute any command, but what about their account actually makes that possible.
- View (but do not edit) the contents of /etc/suduoers. Search for your user account. You won't find them.
- Check the contents of /etc/passwd and /etc/group for entries with your user account. Is there anything different between your account and ops245_1?
- You should find that your user is part of a secondary group. What group is it? Are they part of that group on centos3?
- The wheel group represents administrators with complete sudo privileges. Go back to /etc/sudoers and read the entry for wheel. It should look something like this:
%wheel ALL=(ALL) ALL
- This means that anyone who is part of that group can run any command, as any user. Effectively, they can use sudo to be root.
- So why not just give those admins the root password?
- During the lecture, you should have learned some reasons to limit access to the actual root account, and why using sudo is a better practice. Record your observations.
- On centos3, add your user to wheel as a secondary group so you can use sudo the same way there that you can on your other machines.
Part 2: Adding Limited Sudo Capabilities to Other Users
The wheel group is very useful for senior admins who should be able to run any command, but what about admins who haven't demonstrated the responsibility necessary to wield that power yet? We can use the sudoer files to give them priveleges to run some commands, but not all. Note: While this could be done in the main /etc/sudoers file, the better practice is to create files for each admin user in the /etc/sudoers.d directory.
- Login as your ops245_1 account. Try to run the command
systemctl restart sshd
- If successful, that command would restart the sshd service on that machine, but that user does not have permission to do that.
- Try running that command again, this time with sudo.
- It still won't work, because this user does not have permission to use sudo for anything.
- Create a file called ops245_1 in /etc/sudoers.d. Add the following line to it:
ops245_1 ALL=(ALL) /usr/bin/systemctl- This indicates this user can use sudo to run systemctl commands as if they were any account (root is the important one).
- Try restarting sshd again. This time it should work.
- Change to your ops245_2 account, and try restarting sshd (with and without sudo).
- That account still can't. Sudo entries only affect the users and groups listed.
- We don't want ops245_2 to manage services, that's a job for ops245_1, but we do want them to manage user accounts. So create a sudeors file for ops245_2 and set it so that they can run the useradd, usermod, userdel, groupadd, groupmod, and groupdel commands through sudo.
- Test to make sure it works.
INVESTIGATION 3: Managing System Services and Run-levels
Part 1: How do we Manage System Services?
At the beginning of this lab we mentioned that running unneeded packages can be a security risk due to the unnecessary increase in the complexity of your system. Similarly, it is also unnecessarily hazardous, and even more so, to leave unneeded services running. In this investigation, we will learn how to control services, and turn off those services that we think are not necessary to help reduce security risks.
Although there is a command called: service that may appear to manager services on your Linux system, it is considered deprecated (i.e. "obsolete"). It has been replaced by using the systemctl command.
- Perform the following steps:
- Remain in your centos1 VM for this section.
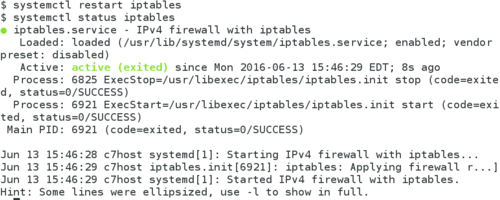
- To verify the status of your iptables service, issue the following command:
systemctl status iptables - Use the commands you used in Lab2 to stop and disable the iptables service.
- Issue a command to verify you disabled and stopped the iptables service.
Note: There is a major difference between stopping a service and disabling a service: If a service is stopped but enabled, the service will start upon reboot. Therefore to prevent it being started upon boot-up, the service will need to be disabled as well! - Issue the commands to start and enable the iptables service, and verify that it is started and enabled.
Note: If you performed the commands correctly, the iptables service should be running, and will automatically run upon your Linux machine start-up.
Part 2: How do we Manage Runlevels?
Running Linux servers in graphical mode can make the server vulnerable to penetration (i.e. a potential break-in to the server from unauthorized intruders). The X-windows framework can be vulnerable to attacks when these servers are connected to the Internet. This is why when you install server versions of Linux, they work in text-based mode only. Desktop versions of Linux are then installed on workstations (working in graphical mode) that connect to the Linux server (for security reasons since those servers are closest to the router and the Internet).
The Linux sysadmin can also change the run-level (or state) of a graphical Linux server to run in text-based mode and run the graphical mode by issuing a command when graphic mode is required. The run-level term is now deprecated in Fedora, and will likely be deprecated in RHEL/CentOS at some point as well, but for now this is what the industry is using.
- Perform the following steps:
- Remain in your centos1 VM for this section.
- Issue the following Linux command:
systemctl get-default
Note: The output should read graphical.target - Try the same command on your centos3 VM and observe how the output differs. Go back to your centos3 VM.
- You can use the systemctl isolate command to change the current run-level. See a list of runlevels here.
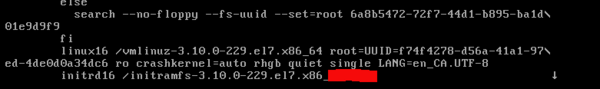
- Change the current run-level in centos1 to multi-user.target by issuing the following command:
sudo systemctl isolate multi-user.target - What did you notice?
- Reboot your centos1 VM. It should return to the graphical login screen. You should notice at this point that the command systemctl isolate did not change the default target the system will boot to.
- Issue the
sudo systemctl set-default multi-user.targetcommand (with elevated permissions) to change the current defatult run-level in centos1 to multi-user.target, then reboot your machine. What do you notice? - Change the current run-level in centos1 to graphical.target by issuing the following command:
sudo systemctl isolate graphical.target - Try to do the same thing to your centos3 VM. Did it work? Why or why not?
- Set the default target on your centos1 VM back to graphical.target before continuing.
Answer INVESTIGATION 3 observations / questions in your lab log book.
INVESTIGATION 4: CREATING USERS VIA SHELL SCRIPTS
Using getopts Function & case statement
We will now use shell scripting to help automate the task for a Linux adminstrator to create regular user accounts.
- Perform the following steps:
- You will be using your c7host machine for this section.
- Open a shell terminal, and login as root.
- Change to the /root/bin directory.
- Download, study, and run the following shell script. Issue the command:
wget https://ict.senecacollege.ca/~ops235/labs/user-create.bash - Try to understand what these Bash Shell scripts do, and then run the script as root to create just one user called test. After running the shell script, view the contents of the /home directory to confirm.
Although the zenity command is a "user-friendly" way to run shell scripts, Linux administrators usually create shell scripts that resemble common Linux commands. In this lab, you will learn to create a shell script using the getopts function to make your shell script behave more like actual Linux commands (including the use of options). Refer to the notes section on the right-hand-side for reference about the case statement and the getopts function.
- Open a Bash shell terminal and login as root.
- Change to the /root/bin directory.
- Use the wget command to download the input file called user-data.txt by issuing the command:
wget https://ict.senecacollege.ca/~ops235/labs/user-data.txt - View the contents on the user-data.txt file to confirm there are 3 fields (username, fullname, and e-mail address)which are separated by the colon (:) symbol.
- Use a text editor (such as
viornano) to create a Bash Shell script called:createUsers.bashin the /root/bin directory. - Enter the following text content into your text-editing session:
#!/bin/bash
# createUsers.bash
# Purpose: Generates a batch of user accounts (user data stored in a text file)
#
# USAGE: /root/createUsers.bash [-i {input-path}]
#
# Author: *** INSERT YOUR NAME ***
# Date: *** CURRENT DATE ***
# Make certain user is logged in as root
if [ $USER != "root" ]
then
echo "Note: You are required to run this program as root."
exit 1
fi
if [ "$#" -eq 0 ] # if no arguments after command
then
echo "You must enter an argument" >&2
echo "USAGE: $0 [-i {input-path}]" >&2
exit 2
fi
- Save your editing session, but remain in the text editor.
- The code displayed below uses the getopt function set the input file pathname or check for invalid options or missing option text. Add the following code
outputFlag="n"
while getopts i: name
do
case $name in
i) inputFile=$OPTARG ;;
:) echo "Error: You need text after options requiring text"
exit 1 ;;
\?) echo "Error: Incorrect option"
exit 1 ;;
esac
done
- Save your editing session, but remain in the text editor.
- The code displayed below uses logic to exit the script if the input file does not exist. Command substitution is used to store each line of the input file as a positional parameter. There is one subtle problem here: The full names of the users contain spaces which can create havoc when trying to set each line as a separate positional parameter. In this case the sed command is used to convert spaces to plus signs (+), which will be converted back later. Finally, a for loop is used to create each account (useradd) and mail the user their account information (mail). Add the following code:
if [ ! -f $inputFile ]
then
echo "The file pathname \"$inputFile\" is empty or does not exist" >&2
exit 2
fi
set $(sed 's/ /+/g' $inputFile) # temporarily convert spaces to + for storing lines as positional parameters
for x
do
userPassWd=$(date | md5sum | cut -d" " -f1)
useradd -m -c "$(echo $x | cut -d":" -f2 | sed 's/+/ /g')" -p $userPassWd $(echo $x | cut -d":" -f1)
mail -s "Server Account Information" $(echo $x | cut -d":" -f3) <<+
Here is your server account information:
servername: myserver.senecac.on.ca
username: $(echo $x | cut -d":" -f1)
password: $userPassWd
Regards,
IT Department
+
done
echo -e "\n\nAccounts have been created\n\n"
exit 0
- Save, set permissions, and then run that shell script for the input text file user-data.txt. Did it work? Try running the script without an argument - What did it do?
- You have completed lab4. Proceed to Completing The Lab, and follow the instructions for "lab sign-off".
Answer INVESTIGATION 4 observations / questions in your lab log book.
LAB 4 SIGN-OFF (SHOW INSTRUCTOR)
Follow the submission instructions for lab 4 on Blackboard.
- Perform the Following Steps:
- Make certain that your c7host, centos1 and centos2 VMs are running.
- Switch to your c7host VM.
- Open a shell terminal, enter a root session, and change to the /root/bin directory.
- Issue the Linux command:
wget https://ict.senecacollege.ca/~peter.callaghan/ops245/labs/lab4-check.bash - Give the lab4-check.bash file execute permissions (for the file owner).
- Run the shell script and if any warnings, make fixes and re-run shell script until you receive "congratulations" message.
- Arrange proof of the following on the screen:
✓ centos1 VM:
✓c7host machine- Demonstrate that this VM 's current run-level is set to 5.
✓ Lab4 log-book filled out.- Run the lab4-check.bash script (must have all
OKmessages)
- Take a screenshot of the proof in the previous step, and upload it and the file generated by lab4-check.bash to blackboard.
Practice For Quizzes, Tests, Midterm & Final Exam
- Describe all of the field in
/etc/passwd - What is the command to create a user? What option to create a home directory for that user?
- What is the command to change the full name of an already-created user?
- What is the command to delete a user account? What option allows for the user's home directory to be removed as well?
- What is the command to create a group? What is the command (or steps) to include a user in a newly-created group?
- What is the purpose of
/etc/shadow? - What is the purpose of
/etc/skel? - What does the term run-level mean?
- How to set the run-level of a Linux system to text-based only? How to set to graphical mode?
- What is the command to view the status of running services?
- What is the command to start a service (like httpd, or sshd)?
- What is the command to stop a service (like httpd, or sshd)?
- What is the difference between starting a service and enabling a service?
- Can a service be stopped and started by issuing just one command?
- What is the purpose of the case statement in shell scripting?
- What is the purpose of the getopts function in shell scripting?
- What type of shell script would be best to automatically create 1200 user accounts (which a list of usernames are stored in a text-file)?