Difference between revisions of "OPS335 Lab 4d"
(→Encrypting Email Connections) |
m (Removing a duplicate paramter.) |
||
| (63 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
| − | = | + | ==LAB RESOURCES== |
| − | + | Online References: | |
| + | |||
| + | * [ Course Notes ] | ||
| + | * [https://en.wikipedia.org/wiki/Transport_Layer_Security TSL, SSL Definition] | ||
| + | * [https://www.e-rave.nl/create-a-self-signed-ssl-key-for-postfix Create a self signed SSL key for Postfix] | ||
| + | * [http://wiki2.dovecot.org/SSL/DovecotConfiguration Dovecot SSL configuration] | ||
| + | |||
| + | |||
| + | == OVERVIEW (ENCRYPTING EMAIL CONNECTIONS)== | ||
| + | |||
| + | |||
| + | |||
| + | Below is the same diagram that we have been referring to over the past 2 email labs: | ||
[[Image:Email-servers.png]] | [[Image:Email-servers.png]] | ||
| − | Note the two globes in the diagram | + | Note the two globes in the above diagram. Those globes represent the Internet that your emails travel through in order to be received by an e-mail recipient. The '''smaller globe (the one your workstation is connected to) cannot be trusted to send mail messages unencrypted'''. The '''larger globe usually involves inter-ISP traffic, often through an internet trunk line, so it is also unencrypted, but it cannot be easily accessed by hackers, pen-testers, or evildoers'''. |
| + | |||
| + | There are '''two important general truths you need to understand about email encryption''': | ||
| + | |||
| + | :* '''Email (the way the vast majority of people use it) travels from SMTP server to SMTP server uncencrypted'''. | ||
| + | |||
| + | :: That means that nothing sent over email is <u>truly</u> secure. But attempting to continually intercepting SMTP server to SMTP server traffic is difficult and expensive, not worth doing for the little bit of money most of us have in our bank account. | ||
| + | |||
| + | :* '''Email travelling over a LAN (especially Wifi, but any local network) is always encrypted'''. | ||
| − | + | :: If e-mail traffic on a LAN was not encrypted, it would be easy and inexpensive to intercept (in order to obtain your username and password). These days, unencrypted connections from your client to your SMTP/IMAP/POP3 server very rarely exist. | |
| − | |||
| − | |||
You see in our diagram that one of the SMTP connections is supposed to be encrypted (this is the one that would be "LAN" traffic) and the IMAP connection as well (this one is either LAN-like traffic or is connecting to localhost, which is a different scenario altogether). | You see in our diagram that one of the SMTP connections is supposed to be encrypted (this is the one that would be "LAN" traffic) and the IMAP connection as well (this one is either LAN-like traffic or is connecting to localhost, which is a different scenario altogether). | ||
| Line 16: | Line 34: | ||
We're going to secure the two connections that we left to be in plain text previously. Unfortunately encrypting things is rarely a straighforward process. Fortunately we have a whole week to spend on it. | We're going to secure the two connections that we left to be in plain text previously. Unfortunately encrypting things is rarely a straighforward process. Fortunately we have a whole week to spend on it. | ||
| − | |||
| − | + | == INVESTIGATION 1: GENERATING A SELF-SIGNED CERTIFICATE == | |
| − | + | According to Wikipedia (https://en.wikipedia.org/wiki/Transport_Layer_Security), '''Transport Layer Security''' (TLS) and its predecessor, '''Secure Sockets Layer''' (SSL), both of which are frequently referred to as 'SSL', are cryptographic protocols designed to provide communications security over a computer network. | |
| − | + | Normally (in production), you would need to pay a "certificate authority" to issue a '''certificate''' for you. That is essentially '''a "signed" public key''' that will tell strangers on the internet that your server is really yours (i.e. the certificate authority says so). There is an obvious problem with the previous statement but that is mainly how public key encryption works on the Internet today. | |
| − | + | We will be generating our own public keys, mainly in order to avoid paying for a certificate. We will not have enough time to get into the details of what all the following commands do in this section. They are from [https://www.e-rave.nl/create-a-self-signed-ssl-key-for-postfix this blog post]. If you don't understand what the blog post refers to but would like to understand in more details, a good recommended book for interest, called Crypto by Steven Levy, provides a more in-depth discussion of encryption and security. | |
| − | <source lang="bash">openssl genrsa -des3 -out andrewsmith.org.key 2048 | + | The public key cryptography concepts in this lab are the same in a previous lab ([http://zenit.senecac.on.ca/wiki/index.php/OPS335_Lab_1#SSH_Keys Lab1: SSH]), although the terminology is slightly different. |
| − | chmod 600 andrewsmith.org.key | + | |
| − | openssl req -new -key andrewsmith.org.key -out andrewsmith.org.csr | + | A simple way to summarize the differences is: |
| − | openssl x509 -req -days 365 -in andrewsmith.org.csr -signkey andrewsmith.org.key -out andrewsmith.org.crt | + | :* The '''.key''' file is your private key. |
| − | openssl rsa -in andrewsmith.org.key -out andrewsmith.org.key.nopass | + | :* The '''.crt''' file is your public key. |
| − | mv andrewsmith.org.key.nopass andrewsmith.org.key | + | |
| + | |||
| + | === Encrypting Postfix with Transport Layer Security (TLS) === | ||
| + | |||
| + | '''Perform the following steps:''' | ||
| + | |||
| + | #Let's start with the "sending" SMTP server we have on VM2. Run the following, replacing <u>andrewsmith.org</u> with '''<u>your</u> domain name''': | ||
| + | |||
| + | <source lang="bash">mkdir -p /root/postfix-keys /etc/ssl/{private,certs} | ||
| + | cd /root/postfix-keys | ||
| + | openssl genrsa -des3 -out vm2.andrewsmith.org.key 2048 | ||
| + | chmod 600 vm2.andrewsmith.org.key | ||
| + | openssl req -new -key vm2.andrewsmith.org.key -out vm2.andrewsmith.org.csr | ||
| + | openssl x509 -req -days 365 -in vm2.andrewsmith.org.csr -signkey vm2.andrewsmith.org.key -out vm2.andrewsmith.org.crt | ||
| + | openssl rsa -in vm2.andrewsmith.org.key -out vm2.andrewsmith.org.key.nopass | ||
| + | mv vm2.andrewsmith.org.key.nopass vm2.andrewsmith.org.key | ||
openssl req -new -x509 -extensions v3_ca -keyout cakey.pem -out cacert.pem -days 3650 | openssl req -new -x509 -extensions v3_ca -keyout cakey.pem -out cacert.pem -days 3650 | ||
| − | chmod 600 andrewsmith.org.key cakey.pem | + | chmod 600 vm2.andrewsmith.org.key cakey.pem |
| − | cp andrewsmith.org.key cakey.pem /etc/ssl/private/ | + | cp vm2.andrewsmith.org.key cakey.pem /etc/ssl/private |
| − | cp andrewsmith.org.crt cacert.pem /etc/ssl/certs/</source> | + | cp vm2.andrewsmith.org.crt cacert.pem /etc/ssl/certs</source> |
| + | |||
| + | ::'''NOTE:''' Those commands will create a certificate, a certificate signing request, a certificate authority, and sign your certificate with your certificate authority.<br>This would be the same as in the real world except there you would contact a real CA, here you're making up your own. | ||
| + | |||
| + | <ol><li value="2">Now, configure Postfix to use the generated certificate, by adding the following to your '''main.cf''' file:</li></ol> | ||
| + | |||
| + | <pre># Settings to enable secure SMTP using my self-signed certificate: | ||
| + | smtpd_tls_auth_only = no | ||
| + | smtpd_use_tls = yes | ||
| + | smtp_use_tls = yes | ||
| + | smtpd_tls_key_file = /etc/ssl/private/vm2.andrewsmith.org.key | ||
| + | smtpd_tls_cert_file = /etc/ssl/certs/vm2.andrewsmith.org.crt | ||
| + | smtpd_tls_CAfile = /etc/ssl/certs/cacert.pem | ||
| + | tls_random_source = dev:/dev/urandom | ||
| + | smtpd_tls_loglevel = 1</pre> | ||
| + | |||
| + | === Setting Up and Testing Encryption with Thunderbird === | ||
| + | |||
| + | '''Perform the following steps:''' | ||
| + | |||
| + | #Currently your Thunderbird is set up to use '''vm2.yoursenecaid.org''' for an SMTP server, with <u>no</u> security. Change that to use '''STARTTLS''' instead (you can change it under '''account settings --> Outgoing Server'''). | ||
| + | # We haven't set up any user authentication, just an encrypted channel;therefore, leave the '''authentication method''' at the value: '''none'''. | ||
| + | #Thunderbird will warn you about the self-signed certificate. You obviously know it's your certificate so you can tell Thunderbird to trust it: | ||
| + | |||
| + | |||
| + | [[Image:SMTP-certificate-warning.png]] | ||
| + | |||
| + | |||
| + | ::'''NOTE:''' Your message may look slightly different (This author, that created the diagram above, made a little mistake when generating the certificate). | ||
| + | |||
| + | <ol><li value="4">After you confirm that security exception, send another email to yourself and make sure you receive it.</li><li> Notice that from the user's point of view nothing is different. But if you were an evildoer trying to steal an identity (the difference is huge). Before it was trivial and now it's computationally prohibitive.</li></ol> | ||
| + | |||
| + | === Encryption Dovecot with Secure Socket layer (SSL) === | ||
| + | |||
| + | Now we will ensure that our '''Dovecot''' connection is secure, and enforce that policy. With SMTP, you will need to allow plain text connections since that is the only method to pass email from server-to-server. With IMAP, there is no server-to-server interaction, but rather only client-to-server interaction. The reason to have an unencrypted IMAP connection would be if your '''IMAP server''' and '''IMAP client''' were the <u>same</u> machine (this would be the situation when using webmail). | ||
| + | |||
| + | '''Perform the following steps:''' | ||
| + | |||
| + | # Let's start by generating a new certificate for Dovecot on your vm3 machine by issuing the following commands: | ||
| + | <source lang="bash">mkdir /etc/ssl/{private,certs} | ||
| + | openssl genrsa -des3 -out vm3.andrewsmith.org.key 2048 | ||
| + | chmod 600 vm3.andrewsmith.org.key | ||
| + | openssl req -new -key vm3.andrewsmith.org.key -out vm3.andrewsmith.org.csr | ||
| + | openssl x509 -req -days 365 -in vm3.andrewsmith.org.csr -signkey vm3.andrewsmith.org.key -out vm3.andrewsmith.org.crt | ||
| + | openssl rsa -in vm3.andrewsmith.org.key -out vm3.andrewsmith.org.key.nopass | ||
| + | mv vm3.andrewsmith.org.key.nopass vm3.andrewsmith.org.key | ||
| + | openssl req -new -x509 -extensions v3_ca -keyout cakey.pem -out cacert.pem -days 3650 | ||
| + | chmod 600 vm3.andrewsmith.org.key cakey.pem | ||
| + | cp vm3.andrewsmith.org.key cakey.pem /etc/ssl/private | ||
| + | cp vm3.andrewsmith.org.crt cacert.pem /etc/ssl/certs</source> | ||
| + | |||
| + | ::'''NOTE:''' This process is identical to what you've done for the vm2 certificate. In fact if your IMAP and SMTP servers are on the same machine (i.e. you can share the certificate between them). In our case, they are not on the same machine. | ||
| + | |||
| + | <ol><li value="2">Next, we need to configure Dovecot to use this for encrypted connections and not allow any kind of plain text connections. Edit the '''dovecot.cont''', '''10-auth.conf''', <u>and</u> '''10-ssl.conf''' files and change the following settings:</li></ol> | ||
| + | |||
| + | <source lang="bash">ssl = required | ||
| + | ssl_cert = <path_to_your_crt_file | ||
| + | ssl_key = <path_to_your_key_file | ||
| + | disable_plaintext_auth = yes | ||
| + | protocols = imaps (instead of imap)</source> | ||
| + | |||
| + | <ol><li value="3">Your key/certificate doesn't have a '''.pem''' extension but they are PEM-encoded files. You can confirm that using the '''file''' command. If you're interested, learning more about configuring Dovecot for SSL, refer to the following documentation: [http://wiki2.dovecot.org/SSL/DovecotConfiguration Dovecot SSL configuration].</li></ol> | ||
| + | |||
| + | === Verifying that Mail Messages are Encrypted=== | ||
| + | |||
| + | '''Perform the following steps:''' | ||
| + | |||
| + | #Use the '''netstat''' command to confirm you're only listening on the '''imaps''' port, and not the plain imap port. | ||
| + | #Next, reconfigure your account settings in Thunderbird to use the '''SSL/TLS''' connection security with your IMAP server. | ||
| + | |||
| + | ::'''NOTE:''' You will get a warning because you're using a self-signed certificate, in that case, make certain to authorize the exception. | ||
| + | |||
| + | '''Record steps, commands, and your observations in INVESTIGATION 1 in your OPS335 lab log-book''' | ||
| + | |||
| + | ==INVESTIGATION 2: OTHER EMAIL CONSIDERATIONS (NOT COVERED IN THIS LAB)== | ||
| + | |||
| + | If you got to this point and everything worked (and you understand what you've done): congratulations, you have set up a working email server and you can now have an intelligent conversation with an employer about this hugely important system. | ||
| + | |||
| + | On the other hand, even though we spent three weeks on e-mail server configuration, we have only performed the simplest possible setup. In the rest of the section, we will only list other commonly-needed services/tools/concepts that we just don't have time for this semester. | ||
| + | |||
| + | Although you are <u>not</u> required to perform any of the operations below, it is recommended to note and understand the following elements to compliment a fully-functioning email system. | ||
| + | |||
| + | === Open Relays === | ||
| + | |||
| + | Your SMTP servers are open relays. That means if they were accessible on the Internet, anyone could use them in order to send spam. This would very quickly get your server blacklisted and you'd have a very hard time getting yourself off that blacklist. | ||
| + | |||
| + | There are two common solutions for that: | ||
| + | |||
| + | *Restrict your "sending" SMTP server to only work on your network. ISPs commonly do this. This doesn't work very well if you have mobile clients (laptops, phones) which are not always connected to your ISPs network. | ||
| + | *Use SASL or some other means of checking that the person trying to use the SMTP server has a valid user on the system. This way only your users will be able to use your server to relay email. | ||
| + | |||
| + | === Sender Policy Framework (SPF) === | ||
| + | |||
| + | '''Sender Policy Framework (SPF)''' uses DNS to publish a list of server IP addresses that are allowed to send email for your domain. In this way, a receiving server can check whether the sending server is authorized (i.e. message is likely not spam) or not (i.e. message is probably spam). | ||
| + | |||
| + | SPF is a pretty cool system, but it's not perfect. It works very well for single servers but if you send mail for your domain from multiple servers (and perhaps a varying number of them), you are required to use wild-cards which reduce the effectiveness of this system. | ||
| + | |||
| + | === DomainKeys Identified Mail (DKIM) === | ||
| + | |||
| + | '''DomainKeys Identified Mail (DKIM)''' is one of several popular spam-prevention measures that use encryption to sign messages originating from your server so that receiving servers can verify that the messages really did come from your server (the keys are published in DNS). | ||
| + | |||
| + | DKIM is considered to be an interesting method, but the strength of the encryption using DKIM is not high. DKIM is a good deterrent against mass amounts of spam, but it doesn't really guarantee other types of attacks on your email server. | ||
| + | |||
| + | === Address Books === | ||
| + | |||
| + | An address book has nothing to do with email, even though you might think they are related systems. Typically, an address book is a completely separate system - using either a '''CardDav''' server (one easy to set up comes with OwnCloud) or an LDAP server. Even tightly integrated services like Microsoft's Active Directory keep the address book separate from the email. | ||
| + | |||
| + | === Vacation Responders === | ||
| + | |||
| + | If you think about it, it is not clear what service should be responsible for sending out vacation messages. Your receiving SMTP server? Do you really want your users to be able to control that? The client? It is probably not running. | ||
| + | |||
| + | It is most likely a separate service. Even though the settings to enable vacation response will usually be next to your other email settings, they will be controlling a separate system that's hooked into your MTA. | ||
| + | |||
| + | === Other Email Features === | ||
| + | |||
| + | There are countless other features and extensions for email. Not to mention proprietary ones like '''Gmail''', '''Yahoo mail''', '''Office 365''', etc. Having mastered the email portion of this course, on the other hand, allows you to evaluate capabilities, design integrated systems, and customize the email service for you organization like no regular email user can attempt to comprehend or understand. | ||
| + | |||
| + | '''Note important considerations not covered in this INVESTIGATION into your OPS335 lab log-book''' | ||
| + | |||
| + | |||
| + | == COMPLETING THE LAB == | ||
| + | |||
| + | Students should be prepared with '''all required commands (system information) displayed in a terminal (or multiple terminals) prior to calling the instructor for signoff'''. | ||
| + | |||
| + | '''Arrange evidence (command output) for each of these items on your screen, then ask your instructor to review them and sign off on the lab's completion:''' | ||
| + | |||
| + | ::<span style="color:green;font-size:1.5em;">✓</span>Thunderbird with a message sent and received using encrypted channels. | ||
| + | ::<span style="color:green;font-size:1.5em;">✓</span>New Thunderbird server configuration for your account. | ||
| + | ::<span style="color:green;font-size:1.5em;">✓</span>Logs on vm2 and vm3 showing the message has been sent and received. | ||
| + | |||
| + | ==EXPLORATION QUESTIONS== | ||
| − | + | #Briefly define the term '''TSL'''. | |
| + | #Briefly define the term '''SSL'''. | ||
| + | #List the steps to setup Encryption for Postfix with TLS. | ||
| + | #List the steps to setup Encryption for Dovecot with SSL. | ||
| + | #List the steps to setup Encryption for the Thunderbird application. | ||
| + | #Provide a brief description of the following terms as they relate to mail servers: | ||
| + | #*'''Open Relay''' | ||
| + | #*'''SPF''' | ||
| + | #*'''DKIM''' | ||
Latest revision as of 09:52, 14 April 2016
Contents
LAB RESOURCES
Online References:
- [ Course Notes ]
- TSL, SSL Definition
- Create a self signed SSL key for Postfix
- Dovecot SSL configuration
OVERVIEW (ENCRYPTING EMAIL CONNECTIONS)
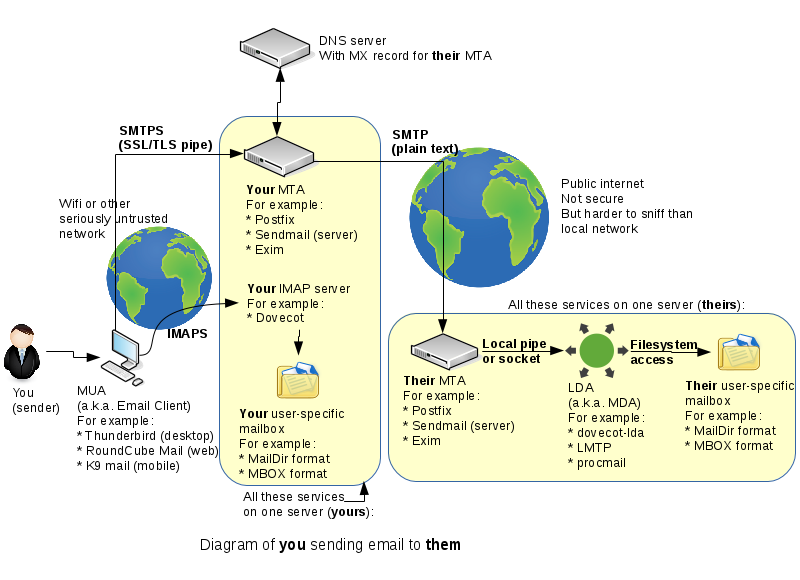
Below is the same diagram that we have been referring to over the past 2 email labs:
Note the two globes in the above diagram. Those globes represent the Internet that your emails travel through in order to be received by an e-mail recipient. The smaller globe (the one your workstation is connected to) cannot be trusted to send mail messages unencrypted. The larger globe usually involves inter-ISP traffic, often through an internet trunk line, so it is also unencrypted, but it cannot be easily accessed by hackers, pen-testers, or evildoers.
There are two important general truths you need to understand about email encryption:
- Email (the way the vast majority of people use it) travels from SMTP server to SMTP server uncencrypted.
- That means that nothing sent over email is truly secure. But attempting to continually intercepting SMTP server to SMTP server traffic is difficult and expensive, not worth doing for the little bit of money most of us have in our bank account.
- Email travelling over a LAN (especially Wifi, but any local network) is always encrypted.
- If e-mail traffic on a LAN was not encrypted, it would be easy and inexpensive to intercept (in order to obtain your username and password). These days, unencrypted connections from your client to your SMTP/IMAP/POP3 server very rarely exist.
You see in our diagram that one of the SMTP connections is supposed to be encrypted (this is the one that would be "LAN" traffic) and the IMAP connection as well (this one is either LAN-like traffic or is connecting to localhost, which is a different scenario altogether).
We're going to secure the two connections that we left to be in plain text previously. Unfortunately encrypting things is rarely a straighforward process. Fortunately we have a whole week to spend on it.
INVESTIGATION 1: GENERATING A SELF-SIGNED CERTIFICATE
According to Wikipedia (https://en.wikipedia.org/wiki/Transport_Layer_Security), Transport Layer Security (TLS) and its predecessor, Secure Sockets Layer (SSL), both of which are frequently referred to as 'SSL', are cryptographic protocols designed to provide communications security over a computer network.
Normally (in production), you would need to pay a "certificate authority" to issue a certificate for you. That is essentially a "signed" public key that will tell strangers on the internet that your server is really yours (i.e. the certificate authority says so). There is an obvious problem with the previous statement but that is mainly how public key encryption works on the Internet today.
We will be generating our own public keys, mainly in order to avoid paying for a certificate. We will not have enough time to get into the details of what all the following commands do in this section. They are from this blog post. If you don't understand what the blog post refers to but would like to understand in more details, a good recommended book for interest, called Crypto by Steven Levy, provides a more in-depth discussion of encryption and security.
The public key cryptography concepts in this lab are the same in a previous lab (Lab1: SSH), although the terminology is slightly different.
A simple way to summarize the differences is:
- The .key file is your private key.
- The .crt file is your public key.
Encrypting Postfix with Transport Layer Security (TLS)
Perform the following steps:
- Let's start with the "sending" SMTP server we have on VM2. Run the following, replacing andrewsmith.org with your domain name:
mkdir -p /root/postfix-keys /etc/ssl/{private,certs}
cd /root/postfix-keys
openssl genrsa -des3 -out vm2.andrewsmith.org.key 2048
chmod 600 vm2.andrewsmith.org.key
openssl req -new -key vm2.andrewsmith.org.key -out vm2.andrewsmith.org.csr
openssl x509 -req -days 365 -in vm2.andrewsmith.org.csr -signkey vm2.andrewsmith.org.key -out vm2.andrewsmith.org.crt
openssl rsa -in vm2.andrewsmith.org.key -out vm2.andrewsmith.org.key.nopass
mv vm2.andrewsmith.org.key.nopass vm2.andrewsmith.org.key
openssl req -new -x509 -extensions v3_ca -keyout cakey.pem -out cacert.pem -days 3650
chmod 600 vm2.andrewsmith.org.key cakey.pem
cp vm2.andrewsmith.org.key cakey.pem /etc/ssl/private
cp vm2.andrewsmith.org.crt cacert.pem /etc/ssl/certs- NOTE: Those commands will create a certificate, a certificate signing request, a certificate authority, and sign your certificate with your certificate authority.
This would be the same as in the real world except there you would contact a real CA, here you're making up your own.
- NOTE: Those commands will create a certificate, a certificate signing request, a certificate authority, and sign your certificate with your certificate authority.
- Now, configure Postfix to use the generated certificate, by adding the following to your main.cf file:
# Settings to enable secure SMTP using my self-signed certificate: smtpd_tls_auth_only = no smtpd_use_tls = yes smtp_use_tls = yes smtpd_tls_key_file = /etc/ssl/private/vm2.andrewsmith.org.key smtpd_tls_cert_file = /etc/ssl/certs/vm2.andrewsmith.org.crt smtpd_tls_CAfile = /etc/ssl/certs/cacert.pem tls_random_source = dev:/dev/urandom smtpd_tls_loglevel = 1
Setting Up and Testing Encryption with Thunderbird
Perform the following steps:
- Currently your Thunderbird is set up to use vm2.yoursenecaid.org for an SMTP server, with no security. Change that to use STARTTLS instead (you can change it under account settings --> Outgoing Server).
- We haven't set up any user authentication, just an encrypted channel;therefore, leave the authentication method at the value: none.
- Thunderbird will warn you about the self-signed certificate. You obviously know it's your certificate so you can tell Thunderbird to trust it:
- NOTE: Your message may look slightly different (This author, that created the diagram above, made a little mistake when generating the certificate).
- After you confirm that security exception, send another email to yourself and make sure you receive it.
- Notice that from the user's point of view nothing is different. But if you were an evildoer trying to steal an identity (the difference is huge). Before it was trivial and now it's computationally prohibitive.
Encryption Dovecot with Secure Socket layer (SSL)
Now we will ensure that our Dovecot connection is secure, and enforce that policy. With SMTP, you will need to allow plain text connections since that is the only method to pass email from server-to-server. With IMAP, there is no server-to-server interaction, but rather only client-to-server interaction. The reason to have an unencrypted IMAP connection would be if your IMAP server and IMAP client were the same machine (this would be the situation when using webmail).
Perform the following steps:
- Let's start by generating a new certificate for Dovecot on your vm3 machine by issuing the following commands:
mkdir /etc/ssl/{private,certs}
openssl genrsa -des3 -out vm3.andrewsmith.org.key 2048
chmod 600 vm3.andrewsmith.org.key
openssl req -new -key vm3.andrewsmith.org.key -out vm3.andrewsmith.org.csr
openssl x509 -req -days 365 -in vm3.andrewsmith.org.csr -signkey vm3.andrewsmith.org.key -out vm3.andrewsmith.org.crt
openssl rsa -in vm3.andrewsmith.org.key -out vm3.andrewsmith.org.key.nopass
mv vm3.andrewsmith.org.key.nopass vm3.andrewsmith.org.key
openssl req -new -x509 -extensions v3_ca -keyout cakey.pem -out cacert.pem -days 3650
chmod 600 vm3.andrewsmith.org.key cakey.pem
cp vm3.andrewsmith.org.key cakey.pem /etc/ssl/private
cp vm3.andrewsmith.org.crt cacert.pem /etc/ssl/certs- NOTE: This process is identical to what you've done for the vm2 certificate. In fact if your IMAP and SMTP servers are on the same machine (i.e. you can share the certificate between them). In our case, they are not on the same machine.
- Next, we need to configure Dovecot to use this for encrypted connections and not allow any kind of plain text connections. Edit the dovecot.cont, 10-auth.conf, and 10-ssl.conf files and change the following settings:
ssl = required
ssl_cert = <path_to_your_crt_file
ssl_key = <path_to_your_key_file
disable_plaintext_auth = yes
protocols = imaps (instead of imap)- Your key/certificate doesn't have a .pem extension but they are PEM-encoded files. You can confirm that using the file command. If you're interested, learning more about configuring Dovecot for SSL, refer to the following documentation: Dovecot SSL configuration.
Verifying that Mail Messages are Encrypted
Perform the following steps:
- Use the netstat command to confirm you're only listening on the imaps port, and not the plain imap port.
- Next, reconfigure your account settings in Thunderbird to use the SSL/TLS connection security with your IMAP server.
- NOTE: You will get a warning because you're using a self-signed certificate, in that case, make certain to authorize the exception.
Record steps, commands, and your observations in INVESTIGATION 1 in your OPS335 lab log-book
INVESTIGATION 2: OTHER EMAIL CONSIDERATIONS (NOT COVERED IN THIS LAB)
If you got to this point and everything worked (and you understand what you've done): congratulations, you have set up a working email server and you can now have an intelligent conversation with an employer about this hugely important system.
On the other hand, even though we spent three weeks on e-mail server configuration, we have only performed the simplest possible setup. In the rest of the section, we will only list other commonly-needed services/tools/concepts that we just don't have time for this semester.
Although you are not required to perform any of the operations below, it is recommended to note and understand the following elements to compliment a fully-functioning email system.
Open Relays
Your SMTP servers are open relays. That means if they were accessible on the Internet, anyone could use them in order to send spam. This would very quickly get your server blacklisted and you'd have a very hard time getting yourself off that blacklist.
There are two common solutions for that:
- Restrict your "sending" SMTP server to only work on your network. ISPs commonly do this. This doesn't work very well if you have mobile clients (laptops, phones) which are not always connected to your ISPs network.
- Use SASL or some other means of checking that the person trying to use the SMTP server has a valid user on the system. This way only your users will be able to use your server to relay email.
Sender Policy Framework (SPF)
Sender Policy Framework (SPF) uses DNS to publish a list of server IP addresses that are allowed to send email for your domain. In this way, a receiving server can check whether the sending server is authorized (i.e. message is likely not spam) or not (i.e. message is probably spam).
SPF is a pretty cool system, but it's not perfect. It works very well for single servers but if you send mail for your domain from multiple servers (and perhaps a varying number of them), you are required to use wild-cards which reduce the effectiveness of this system.
DomainKeys Identified Mail (DKIM)
DomainKeys Identified Mail (DKIM) is one of several popular spam-prevention measures that use encryption to sign messages originating from your server so that receiving servers can verify that the messages really did come from your server (the keys are published in DNS).
DKIM is considered to be an interesting method, but the strength of the encryption using DKIM is not high. DKIM is a good deterrent against mass amounts of spam, but it doesn't really guarantee other types of attacks on your email server.
Address Books
An address book has nothing to do with email, even though you might think they are related systems. Typically, an address book is a completely separate system - using either a CardDav server (one easy to set up comes with OwnCloud) or an LDAP server. Even tightly integrated services like Microsoft's Active Directory keep the address book separate from the email.
Vacation Responders
If you think about it, it is not clear what service should be responsible for sending out vacation messages. Your receiving SMTP server? Do you really want your users to be able to control that? The client? It is probably not running.
It is most likely a separate service. Even though the settings to enable vacation response will usually be next to your other email settings, they will be controlling a separate system that's hooked into your MTA.
Other Email Features
There are countless other features and extensions for email. Not to mention proprietary ones like Gmail, Yahoo mail, Office 365, etc. Having mastered the email portion of this course, on the other hand, allows you to evaluate capabilities, design integrated systems, and customize the email service for you organization like no regular email user can attempt to comprehend or understand.
Note important considerations not covered in this INVESTIGATION into your OPS335 lab log-book
COMPLETING THE LAB
Students should be prepared with all required commands (system information) displayed in a terminal (or multiple terminals) prior to calling the instructor for signoff.
Arrange evidence (command output) for each of these items on your screen, then ask your instructor to review them and sign off on the lab's completion:
- ✓Thunderbird with a message sent and received using encrypted channels.
- ✓New Thunderbird server configuration for your account.
- ✓Logs on vm2 and vm3 showing the message has been sent and received.
EXPLORATION QUESTIONS
- Briefly define the term TSL.
- Briefly define the term SSL.
- List the steps to setup Encryption for Postfix with TLS.
- List the steps to setup Encryption for Dovecot with SSL.
- List the steps to setup Encryption for the Thunderbird application.
- Provide a brief description of the following terms as they relate to mail servers:
- Open Relay
- SPF
- DKIM